Fraudulent Transactions Explained: How to Detect and Handle Refunds
¿Devoluciones?
Ya no es tu problema.
Recupere cuatro veces más devoluciones y evite hasta el 90 % de las que se producen, gracias a la inteligencia artificial y a una red global de 15 000 comerciantes.
Fraudulent transactions have evolved from isolated disputes into a scaled, system-driven problem that quietly erodes merchant revenue. Today, fraud follows predictable patterns: validate, exploit, exit, and shows up across the transaction lifecycle, from checkout to post-delivery disputes like friendly fraud and refund abuse. The real risk isn’t just individual incidents, but the gaps between systems that fraudsters exploit. Effective prevention comes down to recognizing early signals, applying the right controls at each stage, and connecting your checkout, account, and dispute data into a continuous feedback loop that stops losses before they happen.
Fraudulent transactions aren’t a new phenomenon. Medieval merchants faced similar issues. False defect claims, invented shortages, refusal to pay...you name it. The cases were so common that the Lex Mercatoria emerged specifically to keep trade moving and protect sellers from bad-faith buyers.
The dynamic hasn’t disappeared. On the contrary, fraudulent transactions have spiked. What was once settled by guild reputation is now decided by banks, payment processors, and automated dispute systems built with the buyer in mind.
Today, the average merchant loses up to 0.6% of revenue to chargebacks. And for every $1 in fraud losses, the true cost averages over $4 once you include fees, lost inventory, and staff time. According to Juniper, the value of global eCommerce fraud is expected to rise from $44.3 billion in 2024 to $107 billion in 2029, a 141% spike in just five years.
That’s why we’ve crafted this guide. You'll learn how to prevent fraudulent transactions, distinguish a legitimate complaint from an exploit, and respond to cases in a way that protects your revenue without sacrificing the customer relationship.
What Is a Fraudulent Transaction?
A fraudulent transaction is any payment in which the buyer has no real intention of honoring the deal, whether they’re using stolen card details to buy goods they’ll never pay for or using their own card to order products they fully intend to dispute later.
Fraudulent transactions don’t happen randomly. They follow patterns. They exploit gaps across systems such as identity, checkout, fulfillment, and policy. And once you recognise them, you’ll start seeing the signals. Understanding these sequences helps you spot risks early.
How Fraudulent Transactions Occur
At the most fundamental level, fraud is a business model. And so fraudsters do not rely on luck. They execute predictable playbooks that target loopholes between the moment an order is placed and the moment you process a refund.
Before a fraudster places a single order, they’ve already done the math.
Stolen card data has a market price, typically a few dollars per record on dark web marketplaces, and much less for bulk purchases. A fraudster buying a thousand card numbers is making an investment. And like any investment, the return depends on how efficiently they can convert that data into goods or cash before the cards are cancelled. Speed and scale are the operative principles.
That’s why fraud follows a fairly consistent sequence, regardless of taxonomy. First, validate and confirm the asset is usable, whether that’s a live card, a working set of credentials, or a return policy with an exploitable gap. Then, exploit the asset by converting it into value as quickly as possible. And exit before the merchant, bank, or cardholder responds.
What makes most fraudulent transactions difficult to stop is that each stage is designed to appear normal. Validation transactions are small enough to ignore. Exploited accounts have legitimate transaction history. Disputed orders are even messier because the buyer and the disputing customer are the same.
The fraud is engineered to turn your system against you. The higher your store’s exploitability ratio, the more consistently they succeed.
The sections that follow break down where each stage of this sequence targets your operation specifically, and what it looks like when it's happening.
Common Types of Fraudulent Transactions
Fraud often appears as a normal order, a routine return, or a familiar customer. By the time you recognise the pattern, the goods and your revenue are often already gone.
The best defense starts with understanding exactly where these attacks occur. Here are the most common types of fraudulent transactions, categorized by when they occur.
At Checkout (Transaction Level)
This remains the highest-volume attack surface for most online businesses. Fraud types include:
- Card-Not-Present (CNP) Fraud: Criminals use stolen card details to place orders in online environments where no physical card is shown. The real cardholder later spots the charge and disputes it.
- Card Testing: Fraudsters run multiple small transactions (often $1-$5) to verify if stolen cards are still valid before scaling up to bigger purchases. A sudden spike in low-value, uniform orders is a signal of impending larger fraudulent orders.
At the Account Level
These attacks exploit the trust you’ve already built with customers. The most common account-level fraud includes:
- Identity Theft: Fraudsters use stolen personal information to create fake or impersonated identities and place orders. The transaction often looks legitimate at first because it’s tied to real (or partially real) details.
- Account Takeover (ATO): A criminal gains access to a real customer’s account through phishing, credential stuffing, or reused passwords. They then use saved payment methods and addresses to make an order, sometimes for high-value items. The account history makes it slip past basic checks, and the real customer eventually disputes the charges.
After Fulfillment (Post-Delivery)
This stage is often the most painful touchpoint for eCommerce merchants. The product is gone, and your leverage is minimal. Standard post-fulfillment transaction fraud includes:
- Friendly Fraud: This often starts with a genuine purchase. The buyer receives the order, decides they want their money back, and realises that disputing through their bank is faster and more reliable than your return policy. Some do it once; a moment of opportunism, or genuine confusion about a billing description they didn't recognise. Others do it repeatedly, across multiple merchants, because they’ve learned that banks default to the cardholder and merchants rarely fight back.
- Refund and Return Abuse: The customer reads your policy, identifies the gaps, and exploits them. A worn item gets returned as defective. A price-match claim gets submitted after a sale ends. A “lost” package conveniently appears after a refund is issued. No stolen credentials. No bank dispute. Just your own policy used against you.
Other Notable Threats
- Business Email Compromise: Fraudsters impersonate a supplier, logistics partner, or even someone on your team to trick you into changing bank details or authorizing fake payments. This impacts your operations directly rather than individual customer orders.
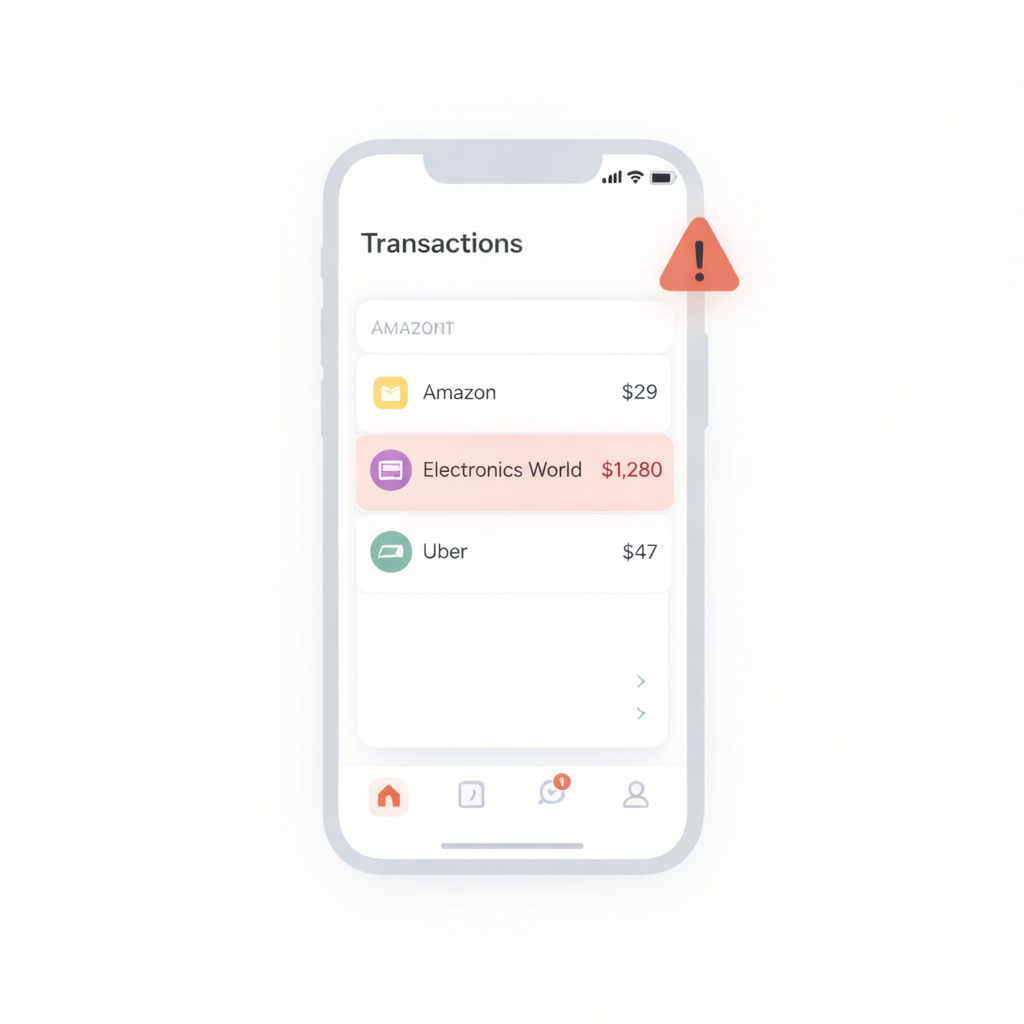
🔥Key Takeaway for Merchants: Many of these fraud types overlap or evolve (a card test can lead to CNP fraud that later turns into a friendly fraud dispute). What matters most isn’t perfect classification. It’s spotting fraudulent transactions early and shutting them down so you can protect your revenue before fulfilling or processing refunds.
How to Detect Fraudulent Transactions
Understanding the types of transaction fraud is only half the job. The other half is recognizing them early enough to act before an order is fulfilled, not after the loss is locked in.
Yet, fraudulent transaction detection isn’t necessarily about catching every bad actor. It’s more about tracking enough high-confidence signals, early enough, to intervene. In practice, these signals cluster around specific stages of the transaction.
At Checkout (Unauthorized Fraud Surface)
Checkout fraud moves fast and at scale, so patterns matter more than individual flags.
Watch for multiple orders placed within a short window from the same IP address, device fingerprint, or shipping address, especially when email addresses change, but other details remain constant.
As highlighted earlier, card testing typically appears as a spike in low-value transactions across multiple cards, often with repeated failures before one succeeds. When a successful payment follows a sequence of small declines, the card is highly likely to be compromised.
Other characteristics provide additional context. For instance, first-time customers placing unusually large orders, buying multiple units of the same high-value item, or requesting expedited shipping without any prior browsing history all align with known fraud patterns. Legitimate customers rarely behave this way without context.
Mismatches between billing address, shipping address, and IP geolocation are not conclusive on their own. However, when all three diverge without a plausible explanation, the probability of fraud significantly increases.
At the Account Level (Compromised Trust)
Account-level fraud is harder to detect because it inherits legitimacy. The account is real. The payment method is saved. The history checks out.
That’s exactly what’s being exploited.
Look for deviations from established behavior. Logins from new devices or locations, especially at unusual hours, are an early signal. A password reset followed immediately by a high-value order is a high-risk sequence. Sudden changes to shipping details on otherwise stable accounts should be treated with caution.
For identity theft at registration, the signals appear earlier. Email addresses that look auto-generated, inconsistencies between customer identity and payment information, or billing information that fails soft verification checks should be flagged before the first transaction is approved.
After Fulfillment (Authorized Fraud Surface)
Post-delivery fraud is rarely visible at the transaction level because the transaction itself is valid.
The detection window here is in the pattern, not necessarily the individual order.
A customer with a history of disputes, whether with your store or across shared fraud networks, represents elevated risk. The same applies to customers with unusually high dispute or return rates across multiple orders.
Timing and behavior also matter. Return requests submitted at the edge of policy deadlines, claims of non-delivery despite confirmed tracking, or repeated “defective” claims on items with no reported issues are all signals that warrant scrutiny before issuing refunds.
For refund abuse, the most useful data sits in your returns workflow, not your fraud dashboard. Customers with disproportionately high return frequency, inconsistent return reasons, or mismatched return addresses may not stand out on a single order. But that becomes obvious when viewed across a sequence of transactions.
Across All Stages
Fraud doesn’t stay confined to one stage. It evolves across the transaction lifecycle.
A card test at checkout can become a successful unauthorized transaction, which later turns into a dispute. Each stage builds on the previous one.
If your fraudulent transaction detection is limited to a single touchpoint, you’ll catch fragments of fraud. When you monitor checkout, account activity, and post-fulfillment behavior as a continuous sequence, you start to see the full pattern and close the exact gaps fraudsters depend on.
How to Prevent Fraudulent Transactions
Preventing fraudulent transactions isn’t a single control. It’s a set of interventions applied at the same points where fraud enters, and the systems to respond when it gets through.
Transaction Level Control
Start with authentication. AVS and CVV checks filter out low-effort fraud and should be standard on every transaction.
For higher-risk orders, 3DS2.2+ standards shift liability to the issuer on properly authenticated transactions. Next is velocity control. Limit how many orders can be placed from a single IP, device, or account within a short window. Flag unusually high-value orders or bulk purchases for review. Restrict expedited shipping on first-time orders.
These controls introduce friction, which makes automated attacks less efficient.
Finally, move beyond static rules. Fraud adapts quickly, and rule-based systems are easy to bypass. Real-time risk scoring, deploying signals such as device fingerprint, IP reputation, and payment behavior, allows you to evaluate each order before it ships.
Because manual review of these multi-point signals is impossible at scale, automated scoring via Chargeflow Prevent becomes a mechanical necessity. It scores transactions at checkout and flags high-risk orders before they become losses.
Account-Level Fraud Prevention Strategies
Fraud prevention starts from account registration. And so requiring verified emails, flagging low-quality or auto-generated identities, and applying identity checks before allowing accounts to transact should be standard practice.
For existing users, enforce multi-factor authentication when login behavior changes, especially in cases of new devices, new locations, or unusual access times. This is one of the most effective ways to stop account takeover.
Track user behavior after login. High-risk sequences, such as a password reset followed by an address change and a high-value order, should trigger review. These are coordinated patterns, not isolated events.
Post Fulfillment Fraud Control Measures
You can’t objectively prevent every dispute. But you can control how you respond.
It starts with building an evidentiary infrastructure. Every order should automatically generate a complete record, including transaction details, delivery confirmation, tracking data, and customer communication. Most disputes are lost not because the merchant is wrong, but due to poor evidence warehousing.
That’s what Chargeflow Automation does efficiently. It handles evidence compiling and submission within the required deadlines. When disputes do occur, you have a reliable, structured, and timely evidence package to auto-submit and win.
Tighten Your Refund Policy
Refund abuse exploits ambiguity. Define return conditions clearly. Specify what qualifies as a defect. Set and enforce return windows. Require proof of purchase, and make it explicit that items returned in a different condition won’t be refunded.
This might seem obvious, but ambiguity is a fraudster’s best friend. Leaving these details to 'common sense' creates a massive liability. If a rule isn't written, it doesn't exist during a dispute." Remove those exploitability gaps and keep experience fair for legitimate customers.
Monitor the Pattern, Not Just the Order
Individual reviews may catch individual cases, but the most expensive fraud appears across patterns.
Track repeat disputes, high return rates, and shifting fraud reasons over time. This is where Chargeflow Insights becomes useful, surfacing trends and repeat offenders that aren’t visible at the order level.
Some fraudulent transactions will be easy to spot in a single transaction, but it becomes unmistakable when you step back and analyze the sequence.
Fraudulent Transaction Monitoring and Prevention Tools: From Isolated to Connected Systems
At a certain scale, fraud stops being a series of incidents and becomes an operational bottleneck. The challenge is no longer just identifying a “bad” transaction, but maintaining consistent, accurate decision-marking across thousands of orders, accounts, and post-delivery events, simultaneously.
The weakness in most merchant setups is the fragmentation. Not the lack of tools.
When your checkout filters do not talk to your account logs, and your dispute evidence doesn’t inform your risk scoring, you create exploitability gaps. Fraudsters live in these gaps. They know that a merchant might catch a stolen card at checkout. However, they often fail to notice a friendly fraud signal from a 6-month-old account.
The Power of the Feedback Loop
Preventing fraudulent transactions effectively demands a seamlessly connected infrastructure that spans the entire transaction lifecycle, ensuring no gaps are left for exploitation. Instead of isolated features, your defense should operate as a continuous loop:
- At Checkout: Real-time scoring filters high-risk orders before fulfillment.
- During the Lifecycle: Monitoring for account takeovers and behavior shifts.
- Post-Fulfillment: Automating dispute responses and gathering evidence.
- The Intelligence Phase: Using dispute outcomes and return patterns to "train" your checkout filters for the next order.
Integrating the Solution: Chargeflow
Chargeflow is designed specifically to close these gaps by linking every stage of the transaction. Rather than forcing you to jump between dashboards, it creates a unified evidentiary and prevention infrastructure.
- Chargeflow Prevent: Scores every order against a massive global dataset, flagging or canceling high-risk transactions before the goods leave your warehouse.
- Chargeflow Alerts: Provides an "early warning" window at the issuer stage, allowing you to resolve issues before they escalate into formal, revenue-draining chargebacks.
- Chargeflow Automation & Insights: Not only wins disputes through AI-driven evidence submission, but aggregates that data to show you exactly where your policy is being exploited.
En resumen
The goal of fraudulent transactions monitoring is to build a system that makes fraud too expensive and difficult to execute against your store. By connecting your checkout, account, and post-fulfillment data, you shift from chasing lost revenue to proactively strengthening your systems. You turn every transaction into an opportunity to learn and harden your defenses.
¿Devoluciones?
Ya no es tu problema.
Recupere cuatro veces más devoluciones y evite hasta el 90 % de las que se producen, gracias a la inteligencia artificial y a una red global de 15 000 comerciantes.
ARTÍCULOS relacionados
¿Tienes alguna pregunta?
: tenemos las respuestas.
Chargeflow recopila datos de decenas de fuentes externas de forma automática. Esto permite una cobertura mucho mayor y unas tasas de éxito mucho mejores, ya que las pruebas presentadas son mucho más completas y convincentes.
Chargeflow recopila datos como la información de los pedidos, los mensajes de los clientes y los detalles de pago. Se encarga de preparar todo el expediente de reclamación por ti, para que no tengas que mover un dedo.
¡Sí! Chargeflow es compatible con más de 50 procesadores de pagos. Esto significa que dispones de una única herramienta para gestionar todas tus devoluciones, independientemente de cómo proceses los pagos.
Solo pagas un porcentaje de los ingresos que te ayudamos a recuperar. Sin cuotas iniciales, sin suscripciones: solo una tarifa basada en los resultados.
Sí. Chargeflow cuenta con las certificaciones SOC 2 Tipo 2, RGPD e ISO. Utilizamos los más altos estándares de seguridad para proteger tus datos.
¿Necesitas más ayuda?
¿Tienes alguna pregunta? Estamos aquí para ayudarte. Solo tienes que pulsar el botón de chat para iniciar una conversación con el servicio de asistencia.






















%201.svg)






































.png)