Card Testing Attacks: How They Work and How to Prevent Them
¿Devoluciones?
Ya no es tu problema.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Card testing is a low-cost fraud tactic where attackers validate stolen card data using micro-transactions before launching larger attacks. Fueled by billions of compromised records and automated tools, it’s difficult to detect with traditional fraud rules. The key to stopping it is early detection, linking signals across transactions, raising the cost of probing, and responding in real time before fraud escalates. Effective prevention requires both pre-authorization controls (to block testing attempts) and post-authorization intelligence (to identify and act on validated threats) without increasing false positives or operational overhead.
Card testing is a payment fraud tactic used by cybercriminals to validate stolen or synthetic card details and determine which ones are still active and usable.
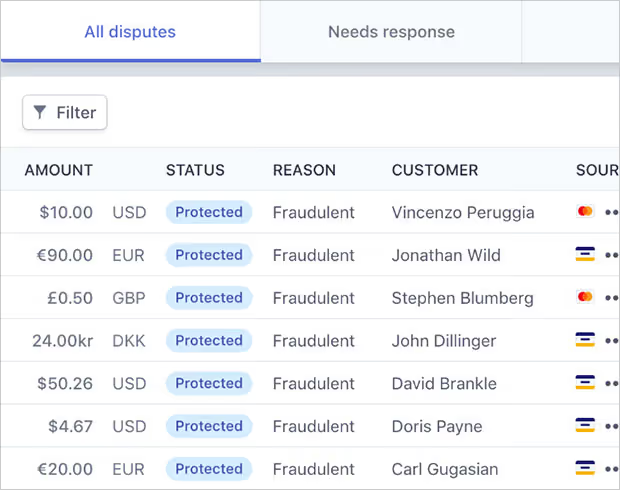
Card testing persists because the supply of compromised data remains vast and constantly refreshed. Last year alone, 142 million stolen card records were listed on dark web marketplaces. While total breach volumes dipped compared to 2024, card fraud hasn’t slowed. It has become even more efficient. Attackers now rely on smaller, higher-quality data sets sourced from infostealer malware and digital skimming operations.
The Identity Theft Resource Center documented 3,322 data breaches in the US alone, affecting over 278 million victims. For merchants, the impact is unmistakable: 33% report experiencing card testing attacks that often result in fees, chargeback risks, and operational strain.
This guide breaks down everything you need to know about card testing attacks, including how they work and how to prevent them effectively.
What Is Card Testing Fraud?
Card testing fraud (also commonly referred to as carding, card cracking, or card validation) is a systematic payment fraud technique used by cybercriminals to confirm whether stolen, generated, or partially known credit/debit details are still active, authorized for use, and have available spending power.
Rather than immediately making large purchases, which carry a higher risk of instant detection and blocking, attackers initiate a series of low-value or even zero-dollar authorization requests. Successful authorizations signal that the card is live and ready for exploitation. Failed attempts help narrow down invalid or canceled cards. This helps them refine the usable dataset for resale or additional fraud.
How Card Testing Attacks Work
At its core, card testing exploits the card-not-present (CNP) environment of online checkouts, mobile apps, donation forms, and subscription services. Because these transactions don’t require the physical card, fraudsters can automate the process at scale using bots, scripts, or specialized card-testing-as-a-service platforms. A single campaign can involve thousands of attempts per minute across multiple merchant sites.
Here’s the typical card testing workflow in four steps:
Step 1: Acquisition: Fraudsters obtain card data through various channels, including large-scale data breaches, phishing and social engineering, malware and infostealers, skimming, or account takeover attacks.
Step 2: Validation: Automated tools submit micro-transactions or authorization-only probes to test key elements like:
- Whether the card number, expiration date, and CVV combination is accepted.
- If Address Verification System (AVS) checks pass (or can be bypassed).
- Available credit or spending limits.
Step 3: Monetization: Confirmed “live” cards are either used for higher-value fraudulent purchases on the same or other sites, converted into gift cards/prepaid instruments, or sold at a premium on underground marketplaces.
Step 4: Escalation: In many cases, testing serves as the gateway to broader attacks, such as making a spree of high-value purchases through compromised accounts or combining with other fraud vectors.
Carding is deliberately low-profile. Small charges often go unnoticed by cardholders (who may dismiss them as minor fees or subscriptions), and many legacy fraud rules are tuned to flag unusually large or suspicious spending patterns rather than high-velocity micro-attempts.
Warning Signs of Card Testing Activity
Card testing signals below are grouped by what they reveal. That’s how they present in practice, and how monitoring tools should be configured to catch them.
Transaction-Level Signals of Carding
- Sudden spikes in micro-transactions. A sharp increase in authorizations between $0.50 and $5, or zero-dollar authorization-only requests appearing in rapid succession. Legitimate customers rarely make repeated micro-purchases within a narrow window.
- Abnormal decline rates. An unusual surge in declines, particularly codes tied to invalid card numbers, expired credentials, AVS failures, or CVV mismatches, is a primary indicator. Attackers test large batches of compromised data, much of which is already canceled or partially known, producing a high delineation-to-approval ratio by design.
- Authorization volume that outpaces actual sales. A widening gap between authorization requests and completed purchases, especially during off-peak hours or periods with no corresponding traffic or campaign activity.
Identity and Source Signals
- Multiple cards from a single origin. Different card numbers attempted from the same IP address, device fingerprint, or browser signature. A genuine customer does not cycle through numerous cards on a single device, making this one of the clearest batch-testing indicators.
- Suspicious or inconsistent customer data. Generic or disposable email addresses, billing information that doesn't align with the card issuer's records, and mismatched billing and shipping addresses. Watch especially for repeated attempts sharing the same Bank Identification Number() range, a strong sign that cards came from the same breach or dataset.
- Geographic anomalies. Transactions originating from regions outside your typical customer base, or from IPs associated with VPNs or proxies. Volume from these sources that doesn't correlate with any recognizable customer segment warrants immediate review.
Señales de comportamiento
- Excessive transaction velocity. Dozens of attempts per minute from a single IP, email, or device, far above any threshold explainable by normal user behavior. Velocity spikes are particularly significant at the micro-transaction level, where basic fraud rules tuned for large purchases often fail to trigger.
- Repeated attempts with minor variations. Fraudsters systematically retry with small changes, cycling through CVV values, expiration dates, or address fields while keeping the core card number constant. Clusters of near-identical attempts are a reliable fingerprint of automated testing tools.
- Behavioral pattern anomalies. Behavioral analytics tools can flag inhuman interaction patterns, such as unnaturally consistent typing speeds, absent mouse movement, or form completions that occur faster than any human could manage. These signals complement transaction data and are increasingly standard in modern fraud stacks.
How These Signals Connect
A wave of low-dollar attempts from a single IP address, producing high declines with repeated AVS failures and shared BIN ranges, is rarely a coincidence. Each signal alone might warrant a second look. Together, they constitute a near-certain indicator of an active card testing campaign.
Early detection depends on tools that analyze linked patterns, not just individual transactions, across IP, device, email, and behavioral data in real-time. Most modern fraud platforms flag these combinations automatically. That allows merchants to take action before a testing probe escalates into high-value fraud or chargebacks.
How to Prevent Card Testing Fraud
The baseline controls of AVS, CVV enforcement, 3DS, and velocity caps are table stakes. How you use card testing signals before the attack matures, and how deliberately you raise the cost of probing without degrading approval rates for legitimate customers, makes all the difference today.
Aquí tienes algunas recomendaciones:
Treat Card Testing Activity as Precursor Intelligence
Card testing is reconnaissance. A cluster of micro-authorization failures from linked BIN ranges and shared device fingerprints signals what’s coming. The same actors, with validated cards, are returning for larger purchases within hours or days. Feed those signals directly into your risk engine as temporary suppression rules to tighten thresholds for testers’ BIN range, IP cluster, or device cohort before the follow-on attack lands.
This requires decline data that’s queryable in near real time, not batched into a morning report. For teams where streaming full transaction records is cost-prohibitive, a metadata-only sidecar stream tracking IP, BIN, and timestamp achieves the same detection capability at a fraction of the infrastructure cost.
Customer Type Indicator (CTI) feeds that track card testing campaigns can provide indicators hours before a wave floods in. But their value depends entirely on how quickly your team can translate an indicator into a live rule. An integration that requires a ticket and a deployment cycle isn’t useful.
Limit What Attackers Learn from Your Responses
Every decline response is feedback. Generic messaging that is indistinguishable from an invalid CVV, expired card, or AVS failure forces attackers to run more attempts to diagnose their own data quality. That friction compounds at scale.
Consider pairing this with randomized latency on suspicious sessions. Testing scripts are optimized for speed. A two or four-second delay on flagged sessions disrupts throughput without affecting legitimate users. Use step-up challenges triggered by velocity or linkage signals specifically, not blanket CAPTCHA, which degrades conversion indiscriminately.
Close the High-Risk Surface Area First
Guest checkout, donation forms, and save-card flows are disproportionately targeted because they require no account context and produce clean authorization signals. These endpoints require their own rule sets. Establish rules like stricter velocity caps, enforce session validation, and regularly audit when your response patterns unintentionally reveal the difference between successful and failed authorizations. Many do.
Manage the False Positive Problem Explicitly
Aggressive defenses suppress legitimate transactions. A rule blocking a BIN range under active testing will also block legitimate cardholders from that issuer. Time-boxed suppression with automated expiry can handle the rule side. However, your customer service team also needs the authority to whitelist a verified user in real time, without routing through the same rule engine that flagged them. If that capability doesn’t exist, every major attack becomes a customer retention problem.
Behavioral biometrics can minimise the false positive problem by distinguishing human sessions from automated ones without relying on card or identity data. They don’t eliminate false positives, which is why the escalation path matters regardless. Track false positive rate as a first-class metric alongside decline rates.
Measure What Actually Matters
Four metrics reveal whether defenses are working:
- Authorization-to-sale ratio. A climbing ratio means testing volume is growing relative to genuine purchases, regardless of how much you’re blocking.
- Decline fees. Processors charge $0.05 to $0.15 per decline. A 50,000-attempt attack, even one fully blocked, can generate over $5,000 in fees before any fraud completes. Suppressing sessions before they reach the gateway is a finance argument as much as a fraud one.
- Conversion impact on low-risk segments. If fraud rates drop at the same time as legitimate conversion, the defense isn’t net positive.
- Time from the first signal to the live rule. If this is measured in hours, you’re always responding to yesterday’s attack.
The Organizational Gap Worth Highlighting
Card testing response spans fraud, engineering, and payment operations, and typically none of them fully owns it. The programs that respond fastest have a single owner and a pre-approved playbook for common attack patterns. It doesn’t need to be sophisticated. It needs to exist and be executable under pressure, without requiring cross-team consensus during an active campaign.
Card Testing Detection and Prevention Tools
The framework above (real-time signal querying, pre-authorization suppression, false positive management, and clear ownership) describes what a mature defense looks like in practice. The harder question is what to build internally versus where external tooling meaningfully extends your capabilities.
Most teams struggle because their systems can’t link signals fast enough, act without coordination overhead, or resolve false positives cleanly. Any tool worth evaluating should be measured against those three constraints.
One approach that aligns with this model is Chargeflow Prevent. It’s useful to be precise about where it fits, and where it doesn’t:
1) Removing Coordination Bottlenecks in Response Workflows
In many organizations, responding to card testing requires a chain of actions: fraud flags a pattern, engineering implements a rule, and operations monitors the impact. That delay, often measured in hours, is where testing campaigns succeed.
A decisioning point that executes actions like cancel, verify, or approve in real time removes that dependency. Instead of escalating between teams, rules are applied immediately at the transaction level. The practical impact is compressed response time, which is the only thing that reliably disrupts active testing.
2) Linking Identity Signals Across Merchants
Most in-house stacks treat signals like IP, device fingerprint, email, and card as independent inputs evaluated per transaction. That works for isolated fraud, but not for coordinated actors reusing infrastructure across multiple merchants.
Network-level systems attempt to solve this by linking these signals into a shared identity graph. In this model, a device or behavioral pattern associated with abuse elsewhere can be recognized before a transaction completes, even if the card itself is new to your system.
The value here isn’t the size of the network, but the transferability of risk signals. It’s how reliably behavior observed in one environment predicts abuse in another, and how quickly that intelligence is applied.
3) Resolving the False Positive Tradeoff Without Manual Intervention
Blocking aggressively is easy. Recovering legitimate customers isn’t.
Most teams stop at detection and leave resolution to customer support (which results in manual reviews, ticket queues, and delayed overrides). That doesn’t scale during an active attack.
A better model introduces a structured verification step at the point of friction. When a transaction is flagged, the buyer confirms ownership through a lightweight flow tied to the cardholder context. If designed correctly, this:
- Preserves conversion for legitimate users
- Generates verifiable audit trails for disputes
- Eliminates the need for manual rule overrides
The important distinction, besides lowering false positives, is creating a resolution path that operates at the same speed as the rule engine.
Where This Approach Does Not Apply
Card testing often begins upstream, at the probe stage. Bots submit authorization attempts before any purchase is completed. This is where decline fees accumulate and where attackers learn from gateway responses.
Controls at this touchpoint, such as rate limiting, session-level blocking, response obfuscation, and latency injection, must be implemented at the gateway or edge. No post-authorization system can prevent those requests from reaching your processor.
This creates a clean separation of responsibilities:
- Pre-authorization: suppress and degrade testing attempts before they hit the gateway
- Post-authorization: evaluate, link, and act on transactions that pass initial checks
Chargeflow Prevent operates in the second approach. It is effective there, but it does not replace the need to harden the first interface.
How to Evaluate in Practice
A meaningful evaluation of card testing prevention tools isn’t based on how many transactions are blocked. It comes down to two questions:
- Does the system surface repeat actors or linked behavior that your current stack misses?
- Can you reduce false positives on legitimate orders without introducing manual review overhead?
If the answer to both is yes, the tool is filling a real gap. If not, it’s another dashboard.
Final Thoughts on Card Testing Attacks
Card testing is an operation problem with a simple economic logic: attackers probe until the cost of probing exceeds the return. Most merchants make this math too easy for fraudsters. Why? Having open endpoints, specific decline feedback, slow response cycles, and no shared intelligence means the cost of testing is effectively zero until damage is already done.
The programs that manage this well do two things well. They’re faster and more deliberate. They treat the first signal as the attack, not the chargeback that follows weeks later. That means, they’ve resolved the organizational ambiguity before an incident forces the question. And they’ve accepted that the false positive problem is as real as the fraud problem, and built for both.
Card testing will continue to evolve. Infostealer-sourced data, AI-assisted enumeration, and testing-as-a-service platforms lower the barrier for attackers faster than most internal controls are updated. The defensive advantage, then, is the speed at which your system learns and responds relative to the speed at which attackers adapt.
If this guide helps you close the gap in the post-authorization cycle, it’s done its job. Get Chargeflow Prevent today.
¿Devoluciones?
Ya no es tu problema.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.






















%201.svg)






































.png)


