Fraude por apropriação de conta (ATO): definição e como evitá-la
Estornos?
Não são mais problema seu.
Recupere 4 vezes mais estornos e evite até 90% dos estornos recebidos, com o apoio da IA e de uma rede global de 15.000 comerciantes.
A fraude por apropriação de conta ocorre quando um fraudador obtém acesso a uma conta real de um cliente e a utiliza para realizar transações não autorizadas. Como a atividade tem origem em uma conta legítima, ela frequentemente contorna as verificações tradicionais contra fraudes e, posteriormente, surge como um estorno. A prevenção da ATO exige mais do que apenas segurança no login. Depende da detecção de comportamentos de risco antes e depois do login, e não apenas do bloqueio das tentativas de acesso.
A fraude por invasão de conta não depende de cartões roubados. Ela depende do acesso.
Um fraudador acessa uma conta de cliente real usando credenciais roubadas ou reutilizadas. A forma de pagamento já está salva. Os dados de entrega já são confiáveis. A transação é concluída sem complicações.
Do ponto de vista do comerciante, parece um pedido normal.
O problema surge mais tarde, quando o cliente contesta a cobrança.
Muitos comerciantes investem pesadamente no bloqueio de fraudes durante o processo de checkout. O ATO contorna essa camada de segurança por completo. O risco começa mais cedo, no momento do login, e continua após o acesso ser concedido.
Compreender como funciona a fraude de apropriação de contas é o primeiro passo.
Para evitar isso, é preciso ir além da autenticação e analisar o comportamento.
O que é a fraude por invasão de conta (ATO)?
A fraude por invasão de conta é um tipo de fraude em que um criminoso obtém acesso a uma conta legítima de um cliente e a utiliza para realizar ações não autorizadas.
No comércio eletrônico, isso geralmente significa fazer pedidos, acessar formas de pagamento cadastradas ou utilizar saldos de conta. Em outros casos, pode envolver a alteração de dados da conta, o resgate de pontos de fidelidade ou o acesso a dados confidenciais do cliente.
A principal diferença em relação à fraude tradicional é o acesso.
Na fraude com cartões roubados, o invasor utiliza diretamente as informações de pagamento. No caso de apropriação de conta, o invasor usa a identidade do cliente dentro de uma conta já existente.
Essa distinção é importante.
As transações provenientes de uma conta com usuário conectado costumam passar pelas verificações antifraude que se concentram no risco de pagamento. O endereço de cobrança bate. O dispositivo pode não parecer suspeito o suficiente para acionar uma recusa.
É por isso que a fraude por invasão de conta geralmente se manifesta como uma transação não autorizada ou um estorno, e não como um pagamento recusado.
Para os comerciantes, isso significa que a perda ocorre após o atendimento do pedido, e não antes da autorização.
Como funcionam os ataques de apropriação de conta
Os ataques de apropriação de conta seguem um padrão simples, mas são eficazes porque se misturam ao comportamento normal dos clientes.
Tudo começa com as credenciais.
Os fraudadores obtêm dados de login por meio de violações de dados, phishing ou testando senhas reutilizadas em vários sites. Isso é conhecido como “credential stuffing”. Em grande escala, mesmo uma baixa taxa de sucesso já é suficiente.
Assim que conseguem acesso, a conta passa a ser o ponto de entrada.
A partir daí, o invasor pode:
- Faça pedidos usando as formas de pagamento salvas
- Alterar endereços de entrega
- Atualize as credenciais da conta para bloquear o acesso do cliente real
- Resgatar valores armazenados, como cartões-presente ou pontos de fidelidade
É aqui que a maioria dos sistemas antifraude perde o controle.

Muitos controles antifraude são projetados para avaliar as transações no momento da finalização da compra. Mas, em um cenário de apropriação de conta, o invasor já está dentro de uma sessão confiável. A transação herda essa confiança.
Não há nenhum indício claro de que a atividade seja não autorizada.
As informações de cobrança estão corretas. A conta possui um histórico. O comportamento pode diferir apenas ligeiramente do padrão habitual do cliente.
É por isso que o ATO é um problema que ocorre após o login.
O risco não termina quando o usuário é autenticado. É aí que ele começa.
E quando o cliente legítimo percebe e entra em contato com o banco, a transação já foi concluída e se transformou em uma contestação.
Técnicas comuns utilizadas em fraudes de apropriação de contas
A invasão de contas não se baseia em um único método. Trata-se de uma combinação de táticas que visam, todas, o mesmo objetivo: obter acesso.
As técnicas mais comuns incluem:
Ataque por preenchimento de credenciais
Os invasores utilizam listas de nomes de usuário e senhas vazados para tentar fazer login em vários sites. Como muitos usuários reutilizam suas credenciais, mesmo uma baixa taxa de sucesso permite o acesso em grande escala.
Phishing
Os clientes são induzidos a compartilhar suas credenciais de login por meio de e-mails, mensagens ou sites de phishing que se fazem passar por marcas legítimas. Assim que as credenciais são obtidas, é possível acessar diretamente as contas.
Troca de cartão SIM
Os fraudadores assumem o controle das contas dos clientes e entram em contato com as equipes de suporte para obter acesso ou redefinir credenciais. Isso lhes permite contornar a autenticação por SMS e redefinir as senhas das contas.
Engenharia social
Os invasores se fazem passar por clientes e entram em contato com as equipes de suporte para obter acesso ou redefinir credenciais. Isso visa explorar falhas nos processos, e não falhas técnicas.
Sequestro de sessão
Em alguns casos, os invasores assumem o controle de uma sessão ativa sem precisar de credenciais de login, muitas vezes por meio de malware ou redes inseguras.
Isoladamente, esses métodos são bem conhecidos. O que os torna eficazes é a consistência.
Eles não precisam comprometer os sistemas. Eles aproveitam:
- senhas reutilizadas
- fluxos de autenticação fracos
- lacunas no monitoramento de contas
- processos de suporte previsíveis
A invasão de contas não consiste em contornar totalmente a segurança. Trata-se de identificar o ponto mais vulnerável na forma como o acesso é gerenciado e mantido.
Sinais de alerta de tentativas de invasão de conta (antes e depois do login)
A maioria dos comerciantes concentra-se nas tentativas de login quando pensa em invasão de contas. Isso é apenas uma parte do quadro.
Alguns dos sinais mais confiáveis surgem após a concessão do acesso, quando a conta já é considerada confiável.
Esses sinais raramente aparecem isoladamente. O risco aumenta quando vários sinais ocorrem na mesma sessão.
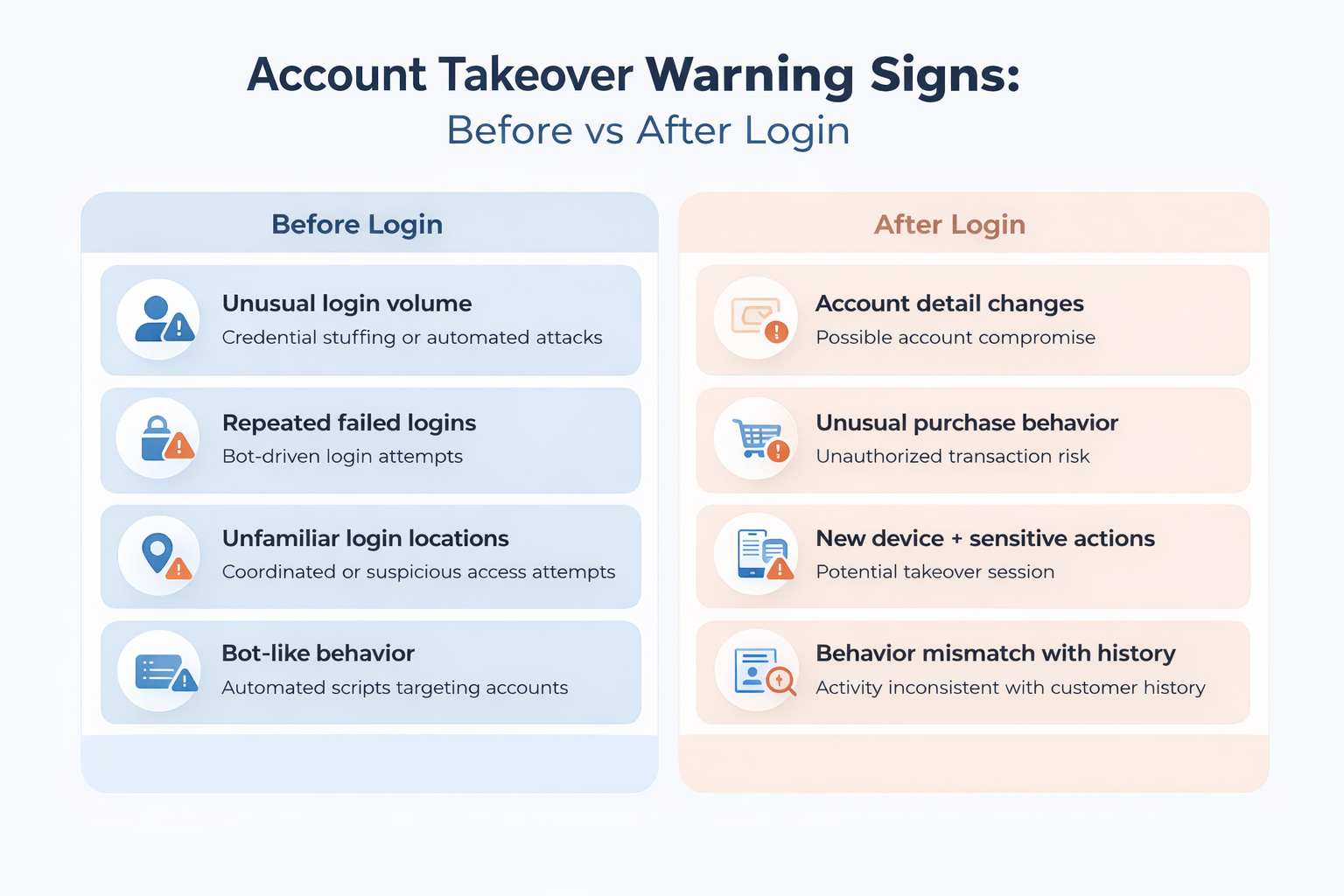
Antes do login: Indicadores precoces
Esses sinais indicam tentativas de acesso. Eles mostram onde os ataques estão ocorrendo, mas não confirmam que houve violação. Algumas tentativas de login ainda serão bem-sucedidas.
Após o login: sinais de alto risco
É aqui que a invasão de contas se torna evidente e onde muitos sistemas apresentam falhas.
Mudanças repentinas nos dados da conta, novos dispositivos acompanhados de atividade ou sequências rápidas de ações costumam indicar que o acesso já foi comprometido.
Sinais isolados podem parecer normais quando considerados individualmente. O risco aumenta quando vários sinais ocorrem na mesma sessão.
A maioria dos sistemas considera o login como o ponto de verificação. No caso de apropriação de conta, o login é o ponto de partida. Se a detecção parar por aí, as atividades de maior risco ficarão sem monitoramento.
Como prevenir fraudes de apropriação de contas
Prevenir a invasão de contas não se resume a implementar uma única medida de segurança. Trata-se de abranger todo o ciclo de vida do processo de obtenção e utilização do acesso.
A maioria dos comerciantes concentra-se na segurança do login. Isso é necessário, mas não é suficiente.
O risco de invasão de contas abrange três etapas: antes do login, durante a autenticação e após a concessão do acesso.
A prevenção contra a invasão de contas funciona como um sistema em camadas ao longo destas três etapas:
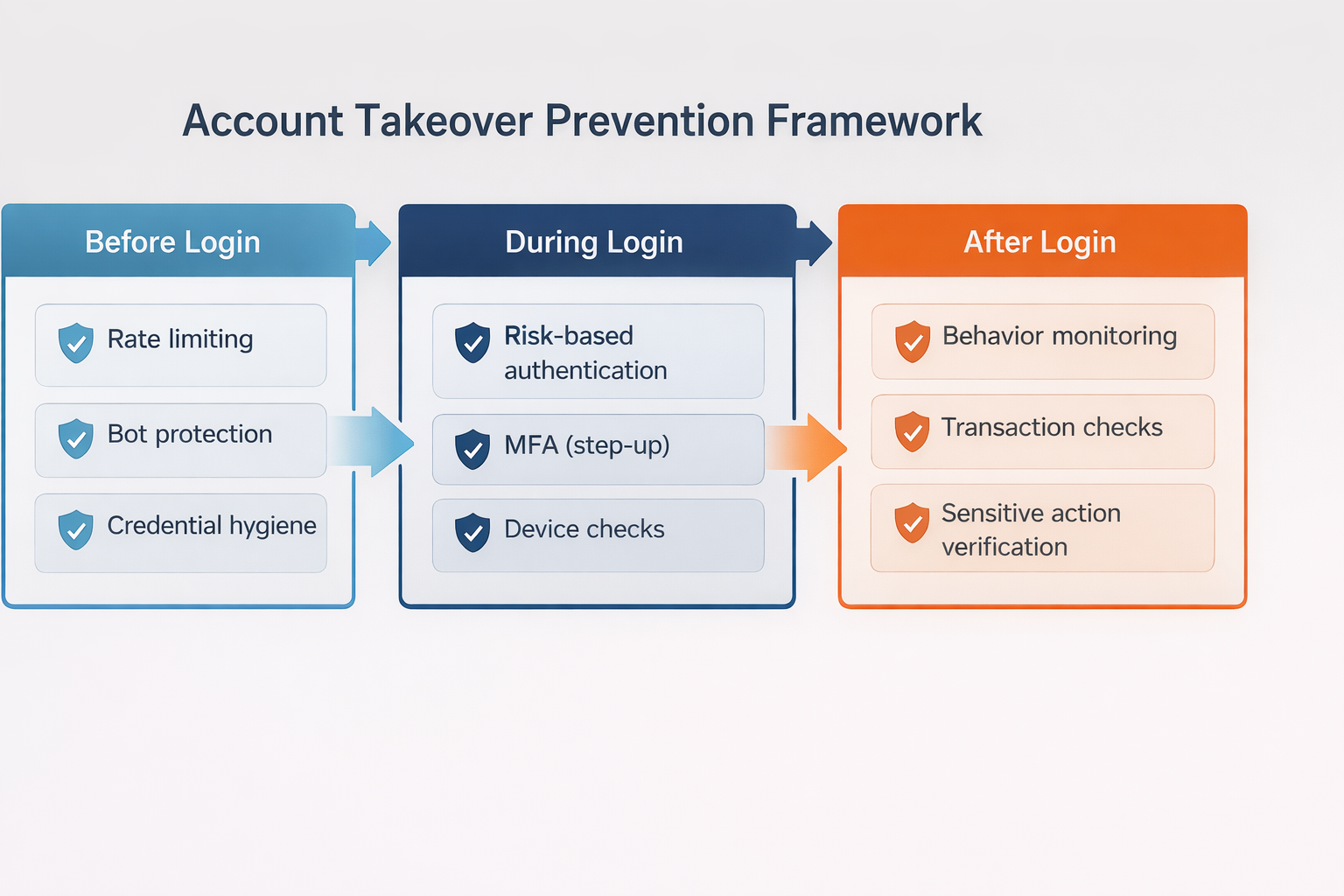
A maioria dos comerciantes investe excessivamente na segurança do login e investe pouco no que acontece depois que o acesso é concedido.
Antes de fazer login: reduza a exposição
É aqui que a maioria dos ataques começa.
Aplicar padrões de autenticação mais rigorosos
Incentive ou exija senhas mais seguras e limite a reutilização de credenciais sempre que possível. Credenciais fracas ou reutilizadas são o ponto de entrada para a maioria dos ataques.
Limitar as tentativas de login automático
A limitação de taxa e a proteção contra bots reduzem a eficácia do credential stuffing, ao retardar ou bloquear tentativas repetidas de login.
Monitorar padrões de login em grande escala
Picos nas tentativas de login em várias contas costumam indicar ataques coordenados, mesmo antes que contas individuais sejam comprometidas.
Essas medidas reduzem o volume, mas não eliminam o risco. Algumas tentativas de login ainda serão bem-sucedidas.
Durante o login: avalie o risco em tempo real
Nem todas as tentativas de login devem ser tratadas da mesma forma.
Utilize a autenticação baseada em risco
Avalie fatores como dispositivo, localização e comportamento para determinar se é necessária uma verificação adicional.
Aplicar a autenticação reforçada de forma seletiva
Aplique verificações adicionais, como a autenticação multifatorial (MFA), apenas quando houver sinais de risco. Isso reduz o incômodo para os usuários legítimos, ao mesmo tempo em que oferece proteção onde é realmente necessário.
Acompanhar a consistência dos dispositivos e das sessões
Dispositivos novos ou não reconhecidos não devem ser tratados da mesma forma que sessões desconhecidas, especialmente no caso de clientes recorrentes.
O objetivo aqui não é bloquear totalmente o acesso. É questionar o acesso quando algo não estiver de acordo.
Após o login: monitore o comportamento continuamente
É aqui que a maioria dos casos de fraude por invasão de contas realmente ocorre.
Uma vez concedido o acesso, a sessão é considerada confiável. As transações, alterações e ações herdam essa confiança, a menos que algo a interrompa.
Fique atento a alterações em contas de alto risco
Alterações no e-mail, na senha ou nos dados de entrega logo após o login são fortes indícios de invasão.
Monitorar o comportamento das transações
Padrões incomuns de pedidos, novos destinos de entrega ou compras repentinas podem indicar atividades não autorizadas.
Introduzir verificações em etapas para ações sensíveis
Exija verificação adicional quando os clientes tentarem realizar ações de alto risco, e não apenas no momento do login.
Comportamento dos links entre sessões
A fraude geralmente envolve uma sequência de ações. Analisar eventos isoladamente faz com que se perca o padrão.
A prevenção não se limita à autenticação. Depende do que acontece depois que o acesso é concedido.
Sistemas de detecção e proteção contra invasão de contas
A detecção de invasão de contas baseia-se em sinais.
Nenhum sinal isolado confirma que uma conta foi comprometida. Os sistemas de detecção funcionam combinando vários sinais relacionados a atividades de login, sessão e transações para identificar comportamentos que não correspondem ao perfil do cliente.
Os sistemas de detecção baseiam-se em três tipos de sinais: comportamentais, de dispositivo e de rede, e de nível de conta.
Sinais comportamentais
Esses sinais se concentram na forma como a conta é utilizada, e não apenas na forma como é acessada.
- Mudanças nos padrões de navegação
- Comportamento incomum da sessão
- Sequências rápidas de ações
- Atividade que não corresponde ao histórico de uso
Os sinais comportamentais costumam ser os mais confiáveis, pois refletem a intenção, e não apenas o acesso.
Sinais de dispositivos e de rede
Isso ajuda a identificar se a sessão corresponde ao ambiente de usuário esperado.
- Dispositivos novos ou não reconhecidos
- Alterações ou inconsistências no endereço IP
- Uso de proxies, VPNs ou redes anônimas
Esses sinais são úteis, mas não são definitivos. Os usuários legítimos também trocam de dispositivos e de localização.
Sinais no nível da conta
Essas alterações se concentram na própria conta.
- Atualizações de senha ou e-mail
- Alterações no endereço de entrega
- Várias tentativas de login malsucedidas, seguidas de uma tentativa bem-sucedida
Esses sinais costumam aparecer logo antes de ocorrerem transações fraudulentas.
Onde os sistemas de detecção apresentam falhas
A maioria dos sistemas de detecção de invasão de contas é mais eficaz no momento do login.
Eles se concentram em:
- bloqueio de ataques de preenchimento de credenciais
- identificar tentativas de login suspeitas
- ativar a autenticação de dois fatores
Isso é necessário, mas deixa uma lacuna.
Depois que o login é bem-sucedido, muitos sistemas reduzem o nível de vigilância. A sessão é considerada confiável, e o monitoramento passa a ser limitado ou inconsistente.
É aí que ocorre a fraude de apropriação de conta.
Os fraudadores não precisam contornar todos os controles. Basta que consigam passar por um único ponto de verificação.
Se a detecção se concentrar apenas no momento do login, ela deixará de identificar a sequência de ações que se segue.
A detecção sem resposta não é suficiente
A detecção por si só não evita perdas.
Identificar comportamentos suspeitos só faz sentido se isso desencadear uma reação:
- autenticação reforçada
- análise de transações
- restrições temporárias à conta
Sem uma camada de resposta, a detecção se torna mera observação.
Uma proteção eficaz depende da capacidade de associar sinais a ações em tempo real, especialmente após o login, quando o risco é maior.
Fraude por invasão de conta e estornos
A fraude por invasão de conta não termina no momento do login. Ela termina com uma transação que o cliente não autorizou.
Do ponto de vista do comerciante, o pedido geralmente parece legítimo. A conta é real. O método de pagamento está cadastrado. A transação passa pelas verificações padrão contra fraudes.
Nesse momento, a transação entra no processo de estorno.
A maioria dos casos de apropriação de conta é classificada como fraude pelos emissores. O titular do cartão alega que não autorizou a transação, e o ônus da prova recai sobre o comerciante, que deve demonstrar o contrário.
É aí que o desafio fica claro.
Ao contrário da fraude tradicional, em que podem surgir sinais suspeitos no momento do pagamento, as transações envolvendo a apropriação de contas se beneficiam da confiança associada a uma conta válida. Sem uma autenticação robusta ou evidências claras que liguem o cliente à transação, é difícil obter sucesso nessas disputas por meio de contestação de estorno.
Em muitos casos, o comerciante tem:
- Login bem-sucedido
- Uma transação concluída
- Dados padrão de pedido e entrega
Mas não há nenhuma prova definitiva de que o próprio cliente tenha autorizado a compra.
Essa lacuna gera prejuízos.
A apropriação de contas também se sobrepõe a outros tipos de disputas. Alguns casos se apresentam como transações não autorizadas. Outros se assemelham à fraude amigável, especialmente quando o acesso à conta é compartilhado ou não está claro. Do ponto de vista do emissor, a distinção importa menos do que a possibilidade de comprovar a autorização.
Para os comerciantes, o resultado é o mesmo.
A receita é perdida após o atendimento do pedido. A contestação contribui para os índices de estorno. O tempo operacional é gasto respondendo a casos com baixa probabilidade de recuperação.
É isso que diferencia a invasão de contas da maioria das categorias de fraude.
A falha não ocorre na fase final. Ela ocorre antes, quando o acesso é concedido sem contexto ou controle suficientes.
Prevenir a invasão de contas não se resume apenas a proteger as contas. Trata-se, antes de tudo, de reduzir o número de transações que acabam gerando contestações.
Os comerciantes que monitoram o comportamento ao longo de todo o ciclo de vida da conta — antes do login, durante a autenticação e após o acesso — reduzem tanto a exposição à fraude quanto os estornos posteriores.
É aí que reside o verdadeiro controle.
A invasão de contas não aparece como fraude no momento do pagamento. Ela surge posteriormente como transações não autorizadas e estornos.
Se você estiver observando contestações relacionadas à atividade da conta, vale a pena verificar como esses casos são tratados depois que ocorrem.
Veja como o Chargeflow ajuda os comerciantes a recuperar receitas de transações não autorizadas e estornos relacionados a ATO.
Estornos?
Não são mais problema seu.
Recupere 4 vezes mais estornos e evite até 90% dos estornos recebidos, com o apoio da IA e de uma rede global de 15.000 comerciantes.
ARTIGOS relacionados
Dúvidas?
. Temos as respostas.
O Chargeflow coleta dados de dezenas de fontes externas de forma automática. Isso permite uma cobertura muito maior e taxas de sucesso muito melhores, pois as evidências apresentadas são muito mais abrangentes e convincentes.
O Chargeflow coleta dados como informações sobre pedidos, mensagens de clientes e detalhes de pagamento. Ele monta um processo completo de contestação para você, sem que você precise fazer nada.
Sim! O Chargeflow é compatível com mais de 50 processadores de pagamentos. Isso significa que você tem uma única ferramenta para todos os seus estornos, independentemente da forma como processa os pagamentos.
Você paga apenas uma porcentagem da receita que ajudamos você a recuperar. Sem taxas iniciais, sem assinaturas — apenas uma estrutura de preços baseada no sucesso.
Sim. A Chargeflow possui certificações SOC 2 Tipo 2, GDPR e ISO. Utilizamos os mais elevados padrões de segurança para proteger seus dados.
Precisa de mais ajuda?
Tem alguma dúvida? Estamos aqui para ajudar. Basta clicar no botão de chat para iniciar uma conversa com o suporte.






















%201.svg)






































.png)


