Counterfeit Card Fraud: Meaning and How to Prevent It
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
EMV chips reduced card cloning but didn't eliminate it. Fraudsters now exploit magnetic-stripe fallback wherever chip reads fail or can be forced. Liability shifts to the merchant when a chip-capable card is processed as a magnetic-stripe transaction, even if a chip reader is present. The earliest warning signs are fallback spikes, terminal tampering, and chargeback reason codes Visa 10.1 and Mastercard 4870 clustering around the same device. Restricting fallback, requiring chip reads, encrypting card data with P2PE, and inspecting terminals daily are the most effective prevention measures.
Counterfeit card fraud was supposed to disappear after EMV chips replaced magnetic stripes. It didn’t.
According to a recent report from the Federal Reserve Bank of Kansas City, 8.0 basis points of every card-present debit transaction on Visa and Mastercard networks are still lost to counterfeit fraud. That percentage may seem small, but for a merchant processing $100 million in annual card-present transactions, that could mean losing up to $80,000 to counterfeit fraud.
Although the fraud rate is lower on regional single-message PIN debit networks (2.2 basis points), counterfeit fraud still exceeds lost or stolen card fraud on dual-message networks.
Even more striking, U.S. card-present fraud rates remain higher than in many other advanced payment markets. Europe reports roughly 0.7 basis points, while Australia sits near 1.0 basis points, according to comparative data cited in the Kansas City Fed’s analysis.
The persistence of counterfeit fraud isn’t an American anomaly, though. Data from the European Central Bank shows that counterfeit cards still accounted for about 11% of non-remote (in-person) card fraud value across the EU and EEA in 2024, even after EMV technology largely dismantled the magnetic-stripe cloning era.
EMV chips made traditional counterfeiting significantly harder. But fraudsters adapted. They perpetrate counterfeit fraud wherever terminals or ATMs fall back to reading the magnetic stripe instead of the chip.
This guide explains what counterfeit fraud is, how it works today, and what merchants can do to stop it. Let’s jump right in!
Counterfeit Card Fraud Liability and EMV Liability Shift
Before October 2015, issuing banks absorbed most counterfeit card fraud losses.
That changed after the EMV liability shift introduced by major card networks, including Visa and Mastercard. The rule is simple: liability falls on whichever party used the less secure technology during the transaction.
In practice:
- If a chip card is processed through the chip, the issuer typically absorbs the fraud loss.
- If the same chip card is processed as a magnetic-stripe transaction, the merchant usually becomes liable.
The critical detail many merchants miss is that liability depends on what actually happened in the transaction, not simply whether a chip reader exists. When a chargeback arrives, card networks review three factors:
- Was the card chip-capable?
- Was the terminal chip-capable?
- Was the transaction processed as a chip read or a magnetic-stripe read?
If a chip-capable card is processed as a magnetic-stripe transaction, especially through fallback, the merchant typically bears the loss.
What Is Counterfeit Card Fraud?
Counterfeit card fraud (also called card cloning) is a type of card-present fraud in which criminals encode stolen payment card data onto a fake physical card, then use it for in-person transactions or ATM cash withdrawals.
They do this anywhere the card is swiped or inserted in person. They obtain the stolen data from the card’s magnetic stripe, typically captured through skimming devices, data breaches, or insider theft. Once encoded onto a blank card, the counterfeit copy swipes just like the real thing.
Counterfeit card fraud is distinct from card-not-present (CNP) fraud, where the perp only needs the card number and never sets foot in your store. With counterfeit fraud, there's a physical fake card in someone's hand at your terminal.
How Counterfeit Card Fraud Works in Card-Present Transactions
The attack follows a three-step process: steal the data, build the card, and use it for an unauthorized transaction.
When the cardholder spots the charge, or the issuer flags it first, a dispute ensues, and the resulting chargeback typically lands squarely on you, the merchant who accepted the transaction.
Common Methods Used in Counterfeit Card Fraud
Let’s break down the counterfeit card fraud process:
Step 1: Data Theft
Criminals target the card’s magnetic stripe, which stores static data. They aim to use this same information for every swipe. The most common data capture methods are:
- Skimmers: They use overlay devices attached to ATMs, gas pumps, or POS terminals to silently read the stripe as the card passes through.
- Data breaches and malware: Orchestrated network intrusion or point-of-sale malware can be used to harvest card stripe data in bulk without any physical device.
- Insider theft: Employees with access to card data or terminal hardware can also be accessories to the crime.
A hidden camera or PIN pad overlay is often paired with a skimmer to capture the cardholder’s PIN. They do this when transactions require PIN authentication.
Step 2: Card encoding
The stolen stripe data, specifically Track 1 and Track 2, the two data layers on every payment card that store the account number, expiration date, and authentication codes, is written onto a blank card. The result is a card that authorizes in the same way as a normal magnetic-stripe transaction would at any terminal reading the magnetic stripe.
EMV chips cannot be cloned this way. Chips generate a unique cryptogram for each transaction that can’t be replicated from stolen data. This is why most counterfeit card fraud today relies on magnetic-stripe transactions or fallback. The terminal or ATM reads the stripe rather than the chip.
Step 3: Fraudulent use
The fake card is swiped at terminals that accept magnetic stripe input, either because the terminal lacks chip capability, the chip read failed, and the fallback kicked in, or the fraudster deliberately triggers a fallback.
Victims might not even notice the crime until the bank statement arrives; the real card never left their wallet.
How Merchants Can Detect Counterfeit Card Activity
Counterfeit card fraud is engineered to look normal. The card appears legitimate, the transaction authorizes on cue, and the payment clears. In many cases, the first sign of fraud is a chargeback weeks later.
Yet counterfeit activity almost always leaves subtle traces: at the terminal, in transaction patterns, and in dispute data. Merchants who actively monitor these signals can often spot compromised devices or cloned card usage before losses escalate.
Here’s how:
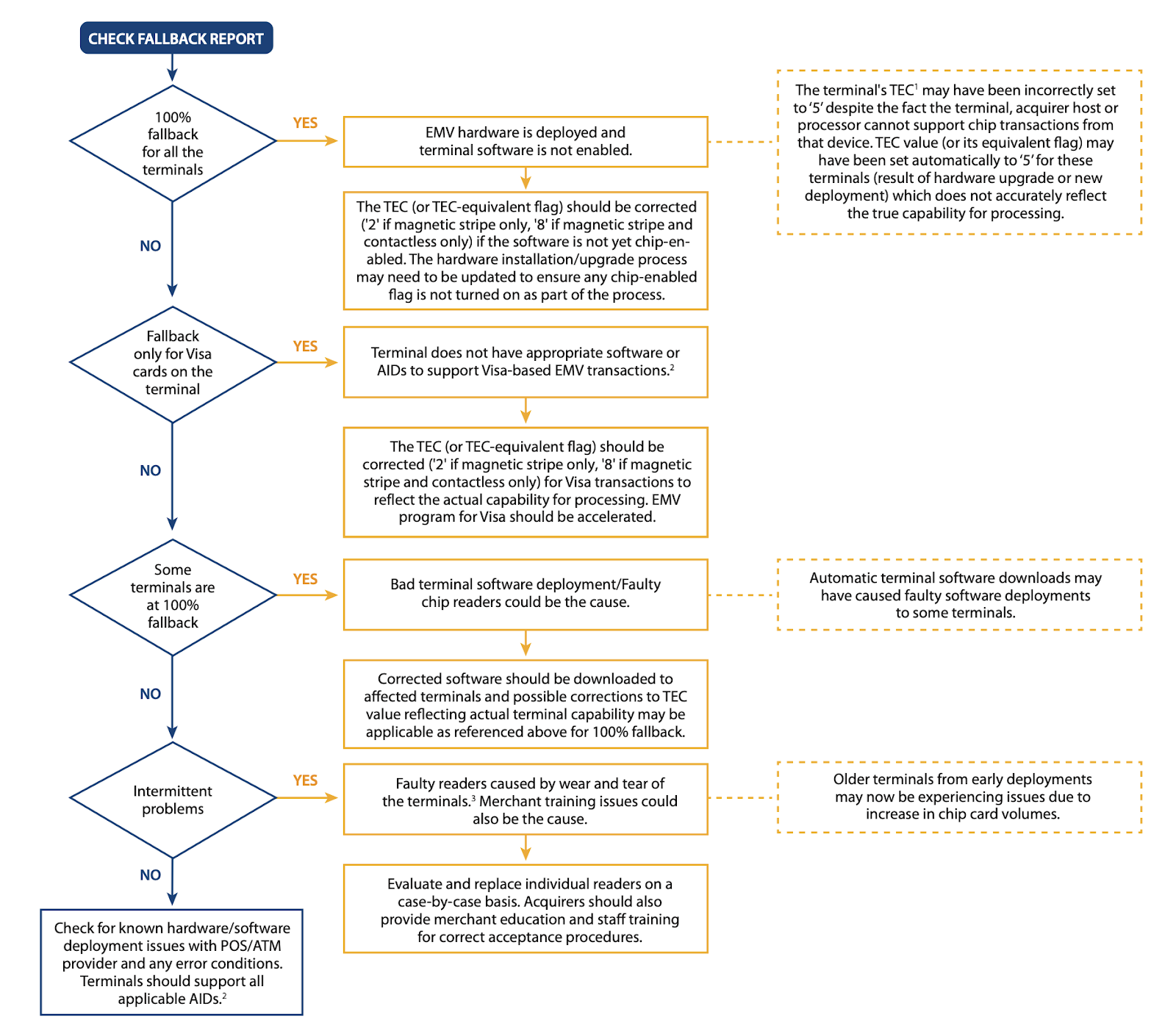
Magnetic Stripe Fallback Transactions
The strongest early warning is an unexpected spike in magnetic-stripe fallback transactions.
EMV chip cards are meant to be dipped. When the chip cannot be read after repeated attempts, the terminal falls back to the magnetic stripe. Occasional fallbacks are normal and can be caused by a damaged chip, a worn reader, or outdated firmware.
But repeated or sudden spikes at the same terminal often signal:
- Tampering or a misconfigured reader
- Criminals who are using cloned magnetic-stripe cards (frequently with intentionally damaged or blank chips to force the fallback).
Visa explicitly warns that fraudsters now deliberately force fallback to bypass chip security, and the associated fraud rate is rising. Acquirers and processors can supply fallback reports by terminal ID. Review them weekly.
Terminal Tampering or Card Reader Modifications
Most counterfeit fraud begins with data theft through skimmers or shimmers installed on or inside the reader. Look for these physical red flags:
- Card reader overlays that are sitting slightly raised above the original hardware.
- Slots that feel loose, tight, misaligned, or sticky.
- PINpads that feel raised, spongy, or flexible.
- Any component that wiggles or detaches when gently tested.
Best Practice: Photograph every terminal (inside and out) on installation day and during routine checks. Compare new photos against the baseline. Subtle differences are often the only clue to a counterfeit card fraud operation.
Unusual Transaction Clusters at Special Terminals
Cloned cards are usually tested before big purchases. Look out for these clues:
- Multiple different cards used in quick succession at one terminal.
- Strings of small “test” authorizations followed by larger amounts.
- Sudden volume spikes at normally quiet devices.
Monitor activity by terminal ID (not just store level) so you can isolate and shut down the affected reader fast!
Unattended Payment Environments
Self-checkouts, parking kiosks, vending machines, and gas pumps are prime targets because oversight is minimal. Look out for these red flags:
- Transaction surges during off-peak hours.
- Clusters of cards that are used within seconds of each other.
- Unusual activity on low-traffic devices.
Chargeback Reason Codes That Signal Counterfeit Activity
When issuers detect counterfeit usage, chargebacks typically arrive under the following reason codes:
- Visa 10.1: EMV Liability Shift Counterfeit Fraud (Card-Present Environment)
- Mastercard 4870: Counterfeit Card Fraud
A cluster of these codes linked to the same terminal or time window is a clear signal that a skimmer was installed or cloned cards were in play.
After-Hours or Low-Security Patterns
Fraudsters love low-spike periods. Flag spikes at night or early morning, sequences of test transactions, or multiple cards in rapid succession.
No single indicator proves fraud, but when physical tampering signs, fallback spikes, transaction clusters, and counterfeit chargeback appear together, the evidence is strong.
Combine daily visual inspections, terminal-level reporting, and proactive chargeback review to catch compromised devices early and stop losses before they multiply.
How to Prevent Counterfeit Card Fraud
Counterfeit fraud succeeds at your terminal because the transaction reads a magnetic stripe instead of a chip. Every prevention measure flows from closing that gap.
Restrict Magnetic Stripe Fallback
Fallback exists for legitimately damaged chips. Fraudsters exploit it deliberately. Contact your acquirer and ask whether fallback can be disabled or restricted on your terminal.
Many merchants never ask. And the answer is often yes. Merchants who restrict fallback see materially lower counterfeit exposure.
Require Chip Reads on all Chip-Capable Cards
Configure terminals to prompt chip insertion first, every time. A genuine chip failure is rare enough that it warrants a staff check, not an automatic swipe.
Prioritize Unattended Terminals
If your outdoor terminals aren’t fully EMV-enabled, make them your highest-priority upgrade. Self-checkout lanes, parking kiosks, and gas pumps remain the most frequently skimmed assets in the U.S. retail industry because there’s no staff to clear or detect tampering.
Deploy Point-to-Point Encryption (P2PE)
P2PE encrypts card data the instant it’s captured inside the terminal. It won’t stop a skimmer from being installed. But it renders any stolen data useless, completely removing your environment as a viable breach target.
Establish a Terminal Inspection Baseline
Photograph every terminal and PIN pad on installation day. Use those images as the daily reference for opening inspections. Check tactilely:
- gentle tug on the reader's face,
- test for unusual give in the PIN pad,
- anything sitting proud of the surrounding hardware.
Regular inspections help detect tampering before stolen data accumulates.
Final Thoughts on Counterfeit Card Fraud and Next Steps
EMV technology dramatically reduced traditional card cloning, but it did not eliminate counterfeit fraud. Instead, criminals shifted their focus to the remaining vulnerabilities in the payment ecosystem, particularly magnetic-stripe fallback, compromised terminals, and unattended payment environments.
Merchants who actively monitor terminal behavior, restrict fallback transactions, and inspect payment devices regularly can significantly reduce their exposure to counterfeit fraud.
Next Steps: Use Chargeback Data to Stop Fallback Transactions
Magnetic-stripe fallback does more than weaken security. It also increases the merchant’s exposure to counterfeit chargebacks.
Clusters of counterfeit chargebacks tied to the same terminal and a short time window almost always point to a skimming event.
That’s where Chargeflow Insights delivers.
This free AI dashboard instantly flags those exact fraud code clusters across all your terminals and processors. Paired with Chargeflow Alerts, you can receive real-time notifications of compromised devices in minutes. Add in Chargeflow Automation, and representment happens on autopilot.
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Related ARTICLES
Questions?
we’ve got answers.
Chargeflow collects data from dozens of third party signals, automatically. This allows for much more coverage and much better win rates because the evidence submitted is much more comprehensive and compelling.
Chargeflow collects data like order info, customer messages, and payment details. It builds a full dispute case for you, so you don’t have to lift a finger.
Yes! Chargeflow works with 50+ payment processors. That means one tool for all your chargebacks, no matter how you process payments.
You only pay a percentage of the revenue we help you recover. No upfront fees, no subscriptions — just success-based pricing.
Yes. Chargeflow is SOC 2 Type 2, GDPR, and ISO certified. We use top security standards to keep your data safe.
need more help?
Have a question? We’re here to help. Just hit the chat button to initiate a conversation with support.






















%201.svg)






































.png)