What Is eCommerce Fraud? Common Types and Best Practices
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
eCommerce fraud rarely announces itself, which is why most incidents go undetected until the damage is done. Fraudsters exploit predictable gaps where incentives outweigh risk, targeting everything from payment flows to post-purchase disputes. The underlying logic is consistent: Incentive × Accessibility × Anonymity ÷ Friction. Where that equation favors the attacker, fraud follows. Detection means reading patterns rather than isolated signals. Prevention means shifting the economics (raising friction, narrowing access, reducing anonymity) until attacks stop being worth the effort. Chargeflow Prevent exists to ensure your defenses scale faster than your exposure.
eCommerce fraud rarely appears chaotic. More often, it masquerades as success: record-breaking sales, soaring approval rates, and expanding global reach. Outwardly, every metric improves while profit margins quietly erode.
As digital commerce scales, so do the incentives to exploit it. Fraudsters are evolving faster than traditional controls. They’re targeting everything from stolen credentials to post-purchase disputes.
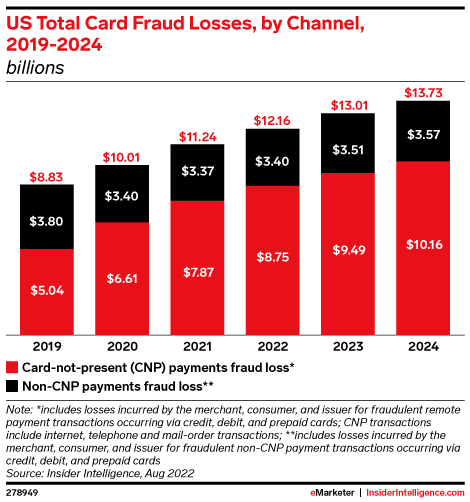
The financial impact is equally severe. Industry estimates indicate that for every $1 lost to fraud, merchants incur at least $4.61 in total costs once chargebacks, operational disruption, and reputational damage are factored in.
Despite global fraud prevention spending projected to exceed $100 billion by 2027, losses continue to rise. This gap between investment and effectiveness is proof that fraud isn’t something you throw money at and hope it goes away.
That’s why we’ve crafted this guide for you. It breaks down the most common forms of eCommerce fraud and outlines practical strategies to reduce risk without undermining the customer experience.
What Is eCommerce Fraud?
In the broadest sense, eCommerce fraud is any and all deceptive acts committed on an online merchant’s platform to obtain financial gain or goods illegally.
But for a modern business, that definition is rather passive. eCommerce fraud is the economic exploitation of digital systems for undeserved gains. It occurs whenever the reward outweighs the cost, effort, and risk of detection. In other words, fraud follows a predictable logic.
We can express this logic as a simple framework, the Exploitability Equation, which quantifies how incentive, accessibility, anonymity, and friction interact:
eCommerce Fraud = Incentive x Accessibility x Anonymity ÷ Friction.
When you view eCommerce fraud from this lens, it ceases to be a glitch in the matrix. You realize it’s a calculated, deliberate exploitation of trust gaps in your checkout flow. Fraud is a business model.
Warning Signs and Red Flags of eCommerce Fraud
Detecting fraud in a high-velocity environment is purely about recognizing contextual anomalies. If you wait for a single, obvious red flag to appear, the exploit has likely already scaled. Instead, effective eCommerce fraud detection relies on identifying compound indicators of platform exploitability.
Here’s how that works:
1) Compound Transaction-Level Indicators
No single risk signal justifies declining a transaction. A VPN, a new email address, an unfamiliar device...each is unremarkable in isolation. The risk compounds when these variables intersect:
- Geographic disconnect: A billing address in one region, an IP address in another, and a shipping destination tied to a known freight forwarder or trans-shipment hub.
- The liquidity filter: Orders where a first-time customer bypasses standard browsing behavior to purchase the maximum allowable quantity of high-resale-value items (e.g., gift cards).
- Identity degradation: High-value transactions paired with “disposable” identity signals, such as email domains registered within the last 30 days or VoIP/burner phone numbers that lack a verified billing history.
- Post-purchase redirection: Immediate requests to modify shipping details or reroute a package through the carrier shortly after the order has been processed. This is a common payment fraud tactic that is used to bypass initial address verification checks.
2) Structural Platform-Level Signals
An unusually high number of refund requests within a specific product category or region, or a monthly chargeback tick, does not definitively mean your platform is under siege. These can often be managed as a linear cost. But when transaction volume reaches record highs, while your net profit per order silently tanks, you’re looking at systemic decoupling. Your platform’s exploitability is being tested.
Monitor these structural shifts to identify this decoupling:
- Approval rate and margin deviation: When transaction approval rates and net margin are in opposite directions, you may be looking at high-velocity eCommerce fraud. This is often inadvertently triggered by policy changes, such as removing a verification step.
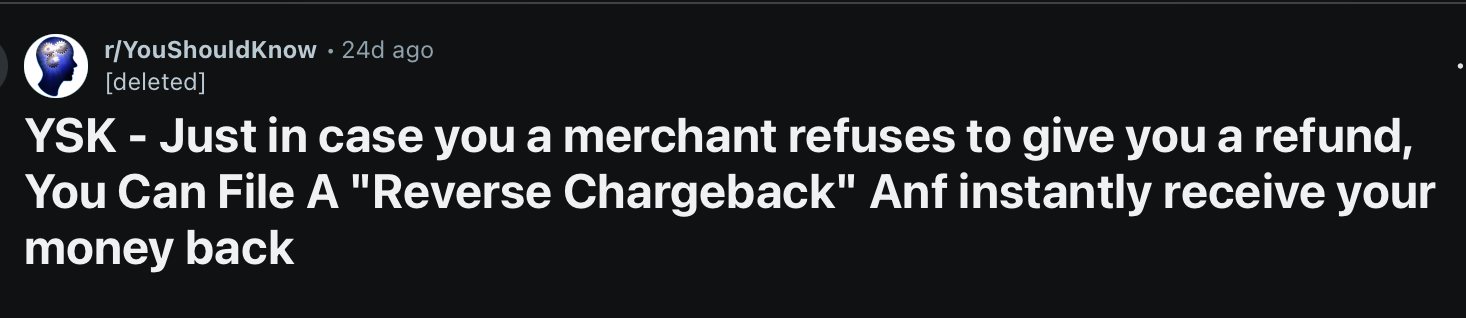
- Refund-to-dispute lag: Data from across the payment ecosystem confirms that denied refund requests often manifest as bank-level chargebacks 2-4 weeks later. This is the classic definition of chargeback fraud, and it is a structural pivot. The claimant exploits the gap between merchant policy and consumer protection rules. When the instigator realizes they cannot bypass your internal gates with fake refund requests, they move to the bank level, where the burden of proof is lower.
- Persistent identity churn: A sudden increase in new accounts sharing the same device fingerprint or hardware ID is a clear indicator of potential fraud. While the names and cards can change, the underlying “digital footprint” remains constant, indicating a coordinated bot-driven attack. Experts have repeatedly warned about this.
- Concentrated promotional abuse: When a small fraction of your user base accounts for a disproportionate volume of promotional redemptions, that should raise an eyebrow. It’s most likely the result of referral loop farming or coupon arbitrage rather than brand loyalty.
With all that said, let’s examine the fraud detection and prevention systems that work for the top 1% eCommerce merchants.
How to Detect and Prevent eCommerce Fraud
To detect and prevent eCommerce fraud, you must view your store the way an attacker would. Why? Because eCommerce fraud is a rational economic activity. It scales only when the math works for the fraudster. It thrives in the space between Conversion (making it easy to buy) and Security (making it hard to steal).
The moment you manipulate the Exploitability Equation variables to make attacking your store more costly than the potential reward, you effectively deter fraudsters from targeting you.
Here are four useful tips to help you detect and prevent eCommerce fraud:
1) Implement Dynamic Friction
Static friction kills growth, but zero friction decimates margins. The solution is dynamic friction; you trigger verification steps in high-exploitability instances.
The logic is simple. Use weighted fraud scores to tax suspicious behavior. You want the cost of the attack to exceed the resale value of the SKU.
2) Harden the Identity Layer
IP addresses and emails are basic variables. Consider focusing on hardware fingerprinting and behavioral biometrics.
- Hardware fingerprinting: Track the underlying Canvas or WebGL fingerprints. As highlighted earlier, fraudsters can spoof 10,000 emails. But they rarely simulate 10,000 unique hardware environments.
- Behavioral cadence: Humans have a “rhythm.” They scroll, hesitate, move the mouse, etc. Bots teleport from “Add to cart” to “Pay Now” in milliseconds. If the behavioral cadence is non-human, trigger a hard block, not just a warning.
3) Close the “Refund-to-Dispute” Loophole
Platforms like Chargeflow enable merchants to neutralize disputes before they formalize. Using pre-fulfillment risk scoring, automated refund triggers, and chargeback deflection, you can quickly intercept high-probability fraud before it reaches the bottom line.
4) Segment Risk by SKU Liquidity
Consider applying stringent verification rules to high-liquidity SKUs that generally attract bad actors. If a product has a 90% resale value on the secondary market, it deserves 90% more scrutiny than the rest of your catalog.
Equally vital, you could limit the number of high-liquidity items a single “digital footprint” can purchase within a 30-day window, regardless of the account name used.
Common Types of eCommerce Fraud Explained
Solving the tension between growth and security requires identifying the attack vectors used to bypass your trust thresholds.
Card-Not-Present (CNP) Fraud
CNP is the baseline of digital theft, which occurs when stolen credit card data is used for transactions. Modern CNP has evolved from stolen numbers to data orchestration. Fraudsters use bots to match stolen card data with leaked “Fullz” (name, DOB, SSN) to pass basic AVS (Address Verification) checks. If your only defense is an expiration date check, you’re essentially wide open.
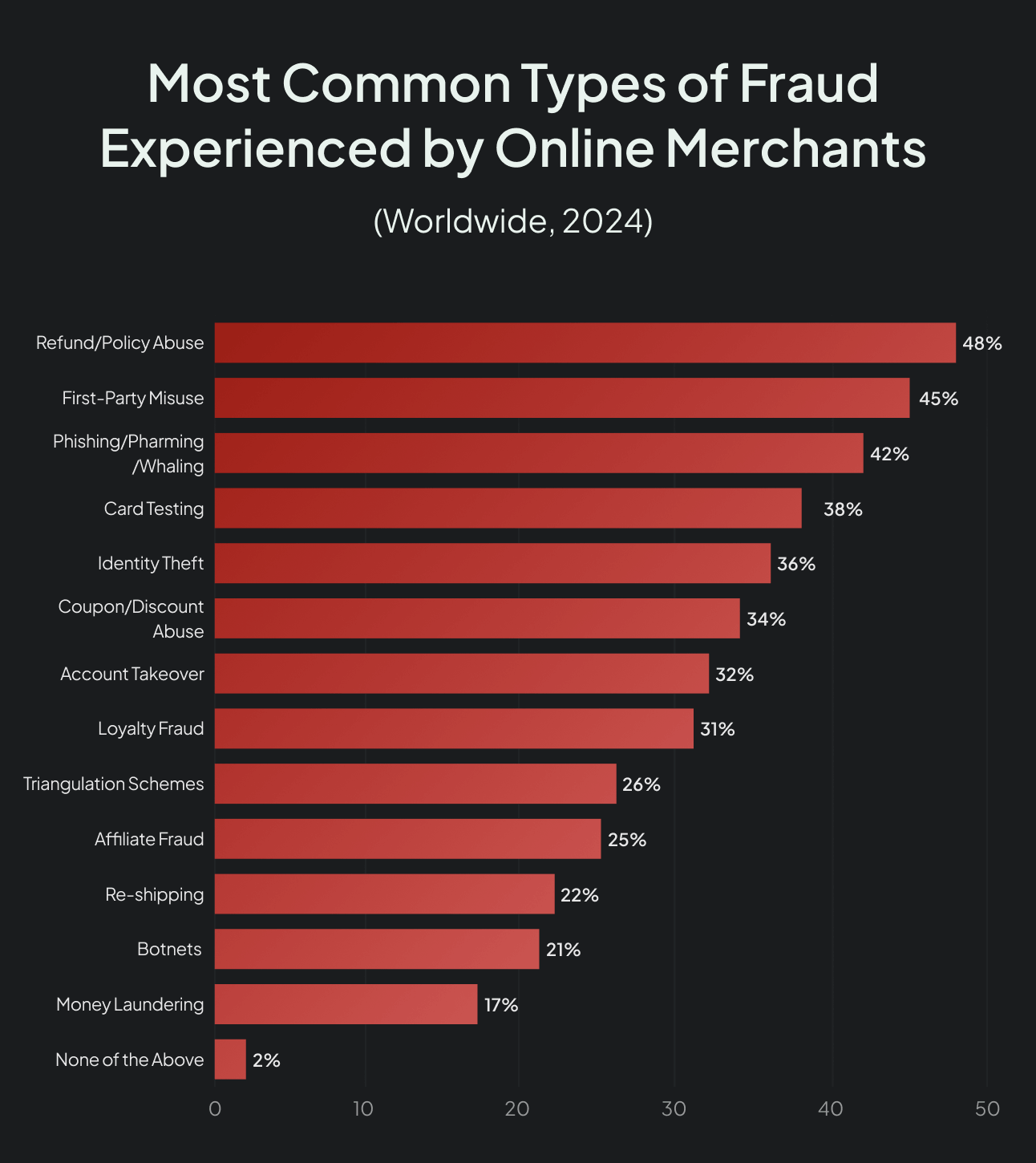
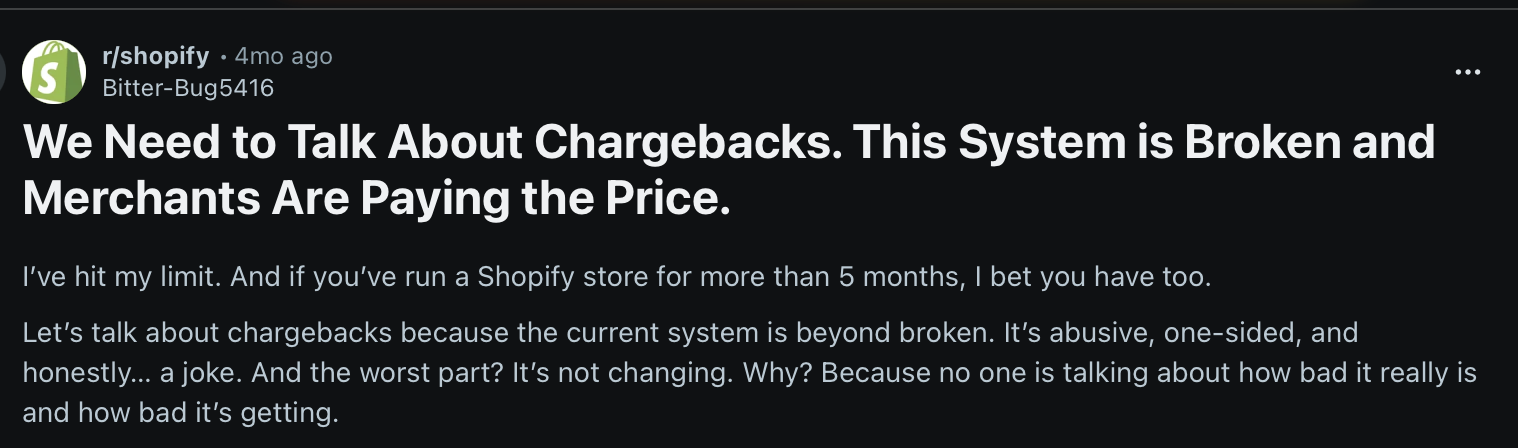
Friendly Fraud (Chargeback Abuse)
When an instigator disputes a legitimate transaction, they are betting on a systemic loophole. They know bank rules are often more lenient than your return policy. Friendly fraud thrives in the grey area where your fulfillment data fails to communicate with the bank’s dispute department. It is less about a product issue and more about policy arbitrage.
Return and Refund Fraud
Exploiting operational lag targets merchants who prioritize “Instant Refunds” over rigorous inspection. Tactics like “wardrobing” (single-use returns), empty-box shipping, or “double-dipping” (claiming a refund while retaining the item) thrive on this speed. Fraudsters bet that your automated system will process the credit before a human in the warehouse discovers the deception.
Account Takeover (ATO) Fraud
In an identity hijack, fraudsters weaponize leaked credentials to access existing customer accounts. By leveraging stored payment methods and loyalty points, they exploit the account’s “Known Good” history to bypass standard filters. The definitive signal isn’t the identity, but the behavioral shift, such as a sudden shipping address or a high-velocity purchase on a dormant account.
Triangulation Fraud
Triangulation fraud is a sophisticated three-step process where you become an unwitting dropshipper for stolen goods:
- A fraudster lists your product at a deep discount on a third-party marketplace.
- A legitimate customer buys the discounted item, providing their real shipping address and “clean” cash to the fraudster.
- The fraudster uses a stolen credit card to buy the item from your store, directing you to ship it to the legitimate customer.
You receive the revenue initially, but the inevitable chargeback from the stolen card will ultimately claw it back. Meanwhile, the fraudster disappears with the clean cash. You’ve lost the inventory, shipping costs, and the dispute fee, all while fulfilling a “sale” for a criminal.
Card Testing and BIN Attacks
This infrastructure probing uses bots to “validate” thousands of stolen card numbers by making micro-purchases on your site to see which ones are active. If your checkout allows unlimited attempts without a CAPTCHA or velocity lock, your platform is being used as a free validation tool for a global fraud syndicate.
Phishing and Social Engineering
This is a human layer exploit where a scammer uses deceptive emails or SMS (Smishing) to trick your staff into revealing sensitive data. It is the easiest way to bypass 2FA or hardware fingerprints. No amount of software can protect you if a customer service rep is tricked into resetting a password for a high-value account without proper verification.
Promo and Gift Card Abuse
Exploiting the liquidity filter involves coupon stacking, referral-loop farming, or using stolen cards to purchase gift cards. Because gift cards function as “digital cash,” untraceable and instantly resalable, they represent the ultimate target for value extraction.
High-volume gift card sales to new accounts rarely signal brand loyalty. Instead, these patterns serve as a primary indicator of money laundering or card draining.
Is Friendly Fraud eCommerce Fraud?
Technically, yes. Yet, strategically, friendly fraud is a policy arbitrage, where a customer exploits the gap between your internal rules and the bank’s more lenient consumer protection policies.
The reason chargeback abuse is problematic for the industry is that the fraud is committed by an actual customer. While third-party fraud involves a criminal, friendly fraud involves a cardholder weaponizing the banking system to bypass your internal controls.
Using AI and Machine Learning to Fight eCommerce Fraud
There’s so much to learn from how PayPal used Machine Learning to solve its fraud issues in the early 2000s. Fraud had surged past 120 basis points (1.2%), draining roughly $12 million a month, about $2,300 every hour. As former marketing director Eric Jackson later wrote in The PayPal Wars, unchecked fraud would have destroyed the company.
Co-founder Max Levchin responded by building “Igor,” an adaptive risk engine blending expert rules with a self-learning neural network, an early commercial big data system. Within months of deploying Igor and CAPTCHA, fraud productivity improved eightfold, even as nearly one-sixth of the company focused full-time on risk. By mid-2001, the fraud rate dropped to 0.49%, then 0.37% by year’s end, which was an industry-leading performance.
AI fraud control didn’t just save PayPal. It secured its dominance.
Connecting AI to the Exploitability Framework
AI is no longer a mere feature, something you toggle on inside a fraud tool. It’s an adaptive decision engine that sits at the center of revenue, risk, and customer experience.
That’s vital to highlight. Traditional “If-Then” rules are static and easily reverse-engineered. Advanced ML models change the dynamics by quantifying uncertainty across hundreds of dimensions in milliseconds.
That’s where the exploitability framework "eCommerce Fraud = Incentive × Accessibility × Anonymity ÷ Friction" comes in.
Here’s how AI affects each variable:
1) Reduces Anonymity: Hardware fingerprinting, behavioral biometrics, and consortium data make it harder for fraudsters to operate with disposable identities. When persistent identity churn becomes detectable, exploitation becomes exponentially more difficult.
2) Increases Friction Selectively: Risk-based authentication applies friction only where needed, raising attacker cost without hurting legitimate customers. The goal is to make the cost of attack exceed the reward.
3) Doesn't Change Incentive: AI can't make your high-liquidity products less attractive to fraudsters. You still need SKU-level risk management and liquidity-based verification rules.
4) Manage Accessibility Dynamically: AI enables you to remain accessible to legitimate customers while becoming progressively more difficult for fraudsters to exploit, the ideal balance between conversion and security.
AI doesn’t necessarily eliminate fraud. It reallocates who absorbs the cost. The key is using AI to rebalance friction and anonymity appropriately across your customer base.
You don’t have to design your own framework like PayPal. Several fraud tools have achieved unparalleled results in leveraging AI and Machine Learning to prevent eCommerce fraud.
Must-Have eCommerce Fraud Prevention Tools
The following specialized tools are the current industry standards for neutralizing fraud at every stage of the funnel:
Final Thoughts on eCommerce Fraud
Stopping eCommerce fraud is primarily about where you choose to deploy money, friction, and risk tolerance inside your business. Every fraud workflow you automate, every dispute you pre-empt, and every approval you protect is a margin decision. You are reclaiming revenue that would otherwise be written off.
The fact is, it’s not eCommerce fraud you should worry about. It’s your response systems that matter. Why? Because you don’t necessarily lose from an attack, but from not knowing which attacks are profitable.
Again, eCommerce fraud rarely explodes overnight. It seeps into contribution margin, hides inside refund rates, and disguises itself as growth. By the time it triggers executive panic, the exploitability curve has already shifted.
The objective is not zero fraud, though. That’s likely a fantasy.
The goal is economic control:
- Keep attacker ROI lower than yours.
- Apply friction where liquidity is highest.
- Close the refund-to-dispute gap before it compounds.
- Monitor margin divergence, not just approval rates.
When you rebalance Incentive x Accessibility x Anonymity ÷ Friction in your favor, fraud reallocates. And when it reallocates away from you, scale becomes durable.
That’s the difference between merchants who manage fraud and merchants who outgrow it. That’s the difference between Chargeflow clients and their counterparts.
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Related ARTICLES
Questions?
we’ve got answers.
Chargeflow collects data from dozens of third party signals, automatically. This allows for much more coverage and much better win rates because the evidence submitted is much more comprehensive and compelling.
Chargeflow collects data like order info, customer messages, and payment details. It builds a full dispute case for you, so you don’t have to lift a finger.
Yes! Chargeflow works with 50+ payment processors. That means one tool for all your chargebacks, no matter how you process payments.
You only pay a percentage of the revenue we help you recover. No upfront fees, no subscriptions — just success-based pricing.
Yes. Chargeflow is SOC 2 Type 2, GDPR, and ISO certified. We use top security standards to keep your data safe.
need more help?
Have a question? We’re here to help. Just hit the chat button to initiate a conversation with support.






















%201.svg)






































.png)
.jpg)

