Unauthorized Transactions: Preventing Credit & Debit Card Fraud
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Unauthorized transactions happen when a payment is made without the cardholder’s permission. They are often the result of account takeover fraud, stolen card data, or gaps in authentication and monitoring. For merchants, the real impact shows up later as disputes and chargebacks. Preventing unauthorized transactions requires more than fraud checks at checkout. It depends on controlling risk before, during, and after the transaction.
Unauthorized transactions are usually treated as isolated fraud events. In practice, they’re the outcome of a chain of failures that unfold over time. A customer account gets compromised, a store payment method is used, and an order proceeds as usual. The dispute comes later.
If you’re trying to understand what a fraudulent transaction is, it helps to look beyond the transaction itself. Unauthorized transactions are not the starting point. They’re the result.
What Is an Unauthorized Transaction?
An unauthorized transaction is any payment made without the cardholder’s knowledge or consent. This can include stolen credit card transactions, fraudulent debit card charges, or purchases made through compromised customer accounts.
Merchants often assume that the card was stolen when they search for "fraudulent transaction meaning" or "what is a fraudulent transaction." That’s only part of the picture.
In many cases, the transaction is technically valid: the correct account is used, the payment method is legitimate, and the system sees a returning customer, which is exactly why these transactions pass standard fraud checks without being flagged.
The issue is authorization. The customer did not approve the transaction, even if the system did.
How Unauthorized Transactions Happen
Unauthorized transactions don’t happen randomly. They follow predictable paths.
The most common is account takeover. A fraudster gains access to a customer account using leaked or reused credentials. Once inside, they can use stored payment methods, change account details, and place orders without triggering suspicion. Everything looks normal because the system trusts the session. That trust removes friction for the customer, but it also removes friction for the attacker.
In one common scenario, a returning customer’s account is accessed using reused credentials. The fraudster logs in, changes the shipping address, and places an order using a stored card. From the system’s perspective, nothing looks unusual. The dispute only comes later.
Other paths include:
- Stolen card data, where card details are used directly without accessing an account.
- Phishing and social engineering, where customers unknowingly provide login or payment information.
- Data breaches and credential reuse, where credentials exposed elsewhere are reused across accounts.
In each case, the transaction itself is the final step, not the initial problem.
Common Causes of Unauthorized Transactions
Unauthorized transactions are driven by a mix of behavior and system gaps.
Customers reuse passwords across multiple sites, making accounts easier to compromise. Stored payment methods reduce friction for customers, but they also reduce friction for attackers. Once access is granted, many systems stop evaluating risk, and limited visibility across sessions makes it harder to detect patterns of abuse.
Most fraud occurs over time. It appears as a sequence. When systems evaluate events in isolation, they miss how those actions connect.
Overreliance on checkout fraud tools leaves gaps, because most systems focus on stolen cards, not compromised accounts.
These aren’t edge cases. They’re structural issues.
How to Detect Unauthorized Transactions Early
Unauthorized transactions are rarely isolated events. They follow patterns, and detection depends on recognizing those patterns early, before they turn into completed transactions.
Detection depends on recognizing those patterns early.
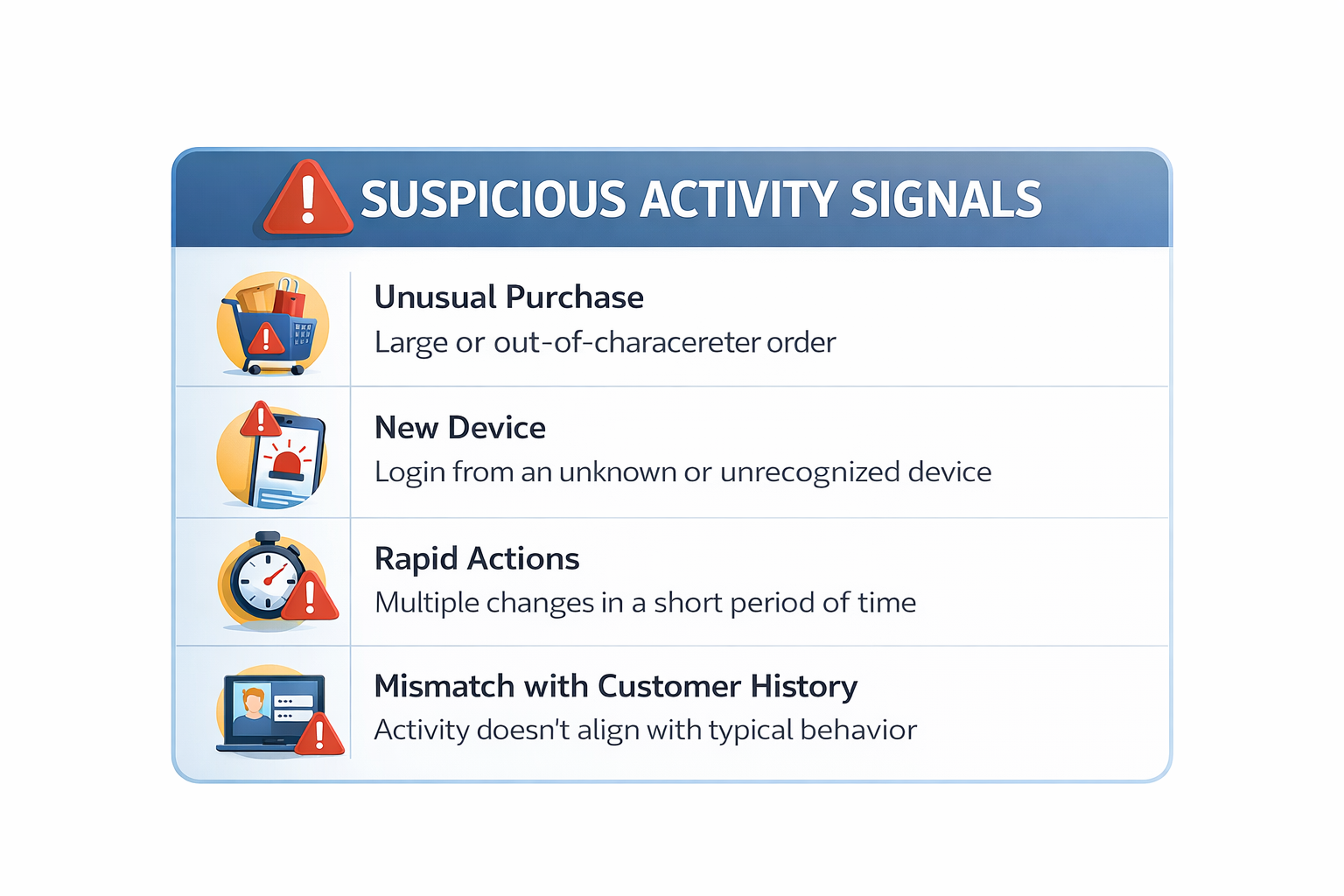
Key signals include:
- Unusual purchase behavior: Orders that don’t match the customer’s typical value, category, or frequency.
- New device followed by activity: A login from an unrecognized device followed by account changes or a transaction.
- Rapid action sequences: Login → account change → purchase within a short window.
- Mismatch between behavior and history: Activity that doesn’t align with how the customer typically interacts.
No single signal confirms fraud, but patterns do. Risk increases when multiple signals appear within the same session or across related activity.
For example, a customer logs in from a new device, changes their shipping address, and places a high-value order within minutes. Each action on its own may look normal. Together, they indicate elevated risk.
How to Prevent Unauthorized Transactions
Preventing unauthorized transactions requires controlling risk across the full lifecycle. Most merchants overinvest in blocking bad payments and underinvest in monitoring trusted sessions.
Unauthorized transaction risk spans multiple stages, not just the moment of payment.
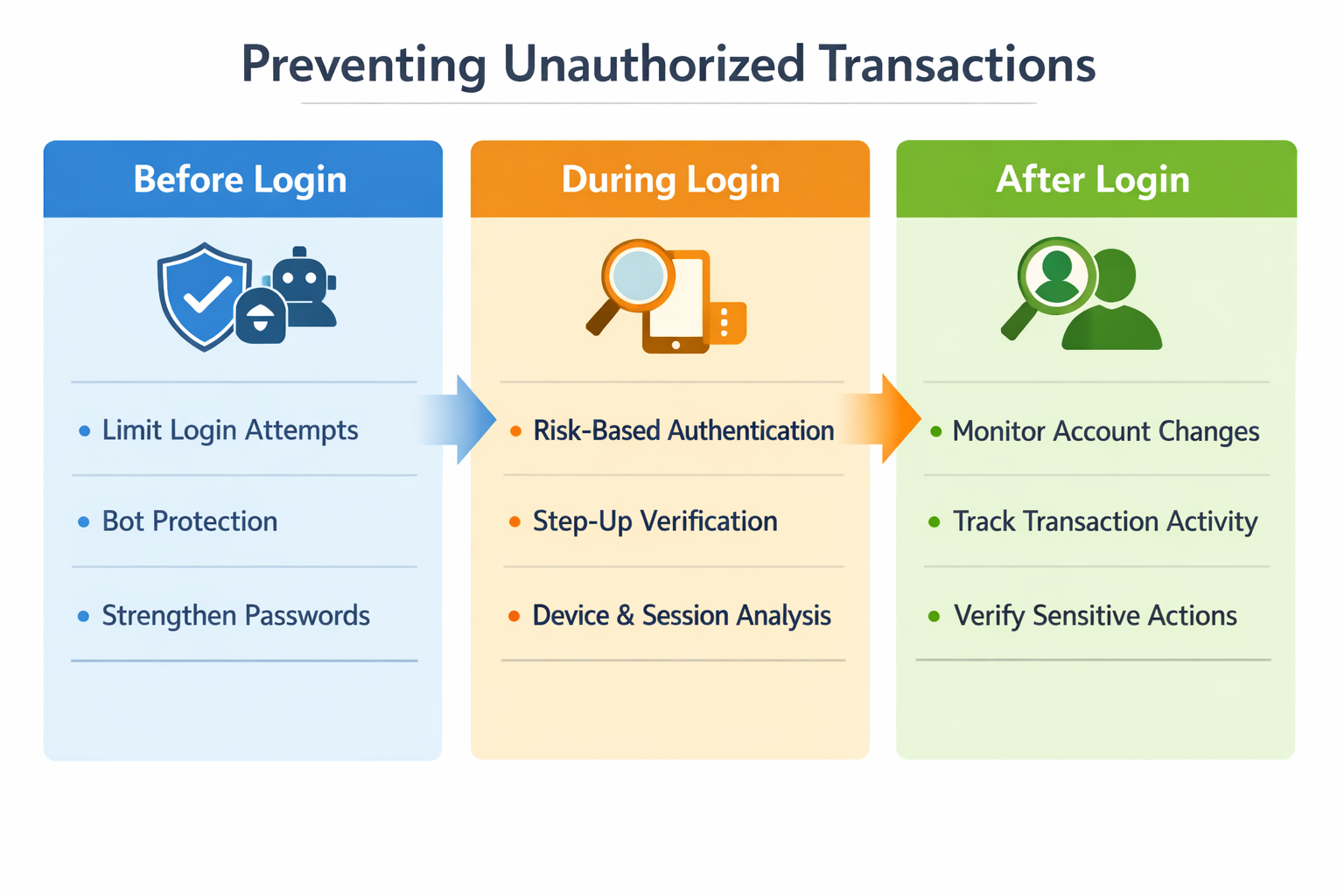
Before Login: Reduce Exposure
Limit automated login attempts, use bot protection, and encourage stronger credential hygiene to reduce the volume of attacks before they begin. These controls reduce attack volume, but they don’t eliminate risk.
During Login: Evaluate Risk
Apply risk-based authentication by evaluating device, location, and behavior signals, and trigger step-up verification only when those signals indicate elevated risk. Track device and session consistency to identify anomalies early.
The goal is not to block access entirely. It’s to challenge access when something doesn’t align.
After Login: Monitor Behavior
This phase is where most unauthorized transactions occur.
Once access is granted, the session is trusted. At that point, fraud is no longer about payment validation. It becomes a behavioral problem.
Monitor account changes, track transaction behavior, and add verification for sensitive actions. Link behavior across sessions, because fraud rarely happens in isolation. It follows a sequence.
Often, the merchant has a successful login, a completed transaction, and delivery confirmation, but no clear evidence that the actual cardholder authorized the purchase. These are the cases that most often turn into lost disputes.
What to Do When a Fraudulent Transaction Occurs
When an unauthorized transaction happens, control shifts away from the merchant.
The customer reports the charge, and the issuing bank takes over the investigation. From that point on, the outcome depends less on the transaction itself and more on how it’s interpreted.
For merchants, the case usually becomes a dispute. Funds are withdrawn, a chargeback is filed, and the burden shifts to the merchant to prove that the transaction was authorized.
That’s where the challenge becomes clear.
Even when the transaction looks legitimate, the account may be valid, the payment method may be on file, and the order may be fulfilled, yet there’s often no definitive proof that the actual customer approved the purchase.
Refunding the transaction early can sometimes prevent a chargeback, but only before the dispute is filed. Once it reaches the issuer, the decision is no longer in the merchant’s hands.
Unauthorized Transactions and Chargebacks
Unauthorized transactions usually avoid immediate friction. The impact shows up later, when the customer notices the charge.
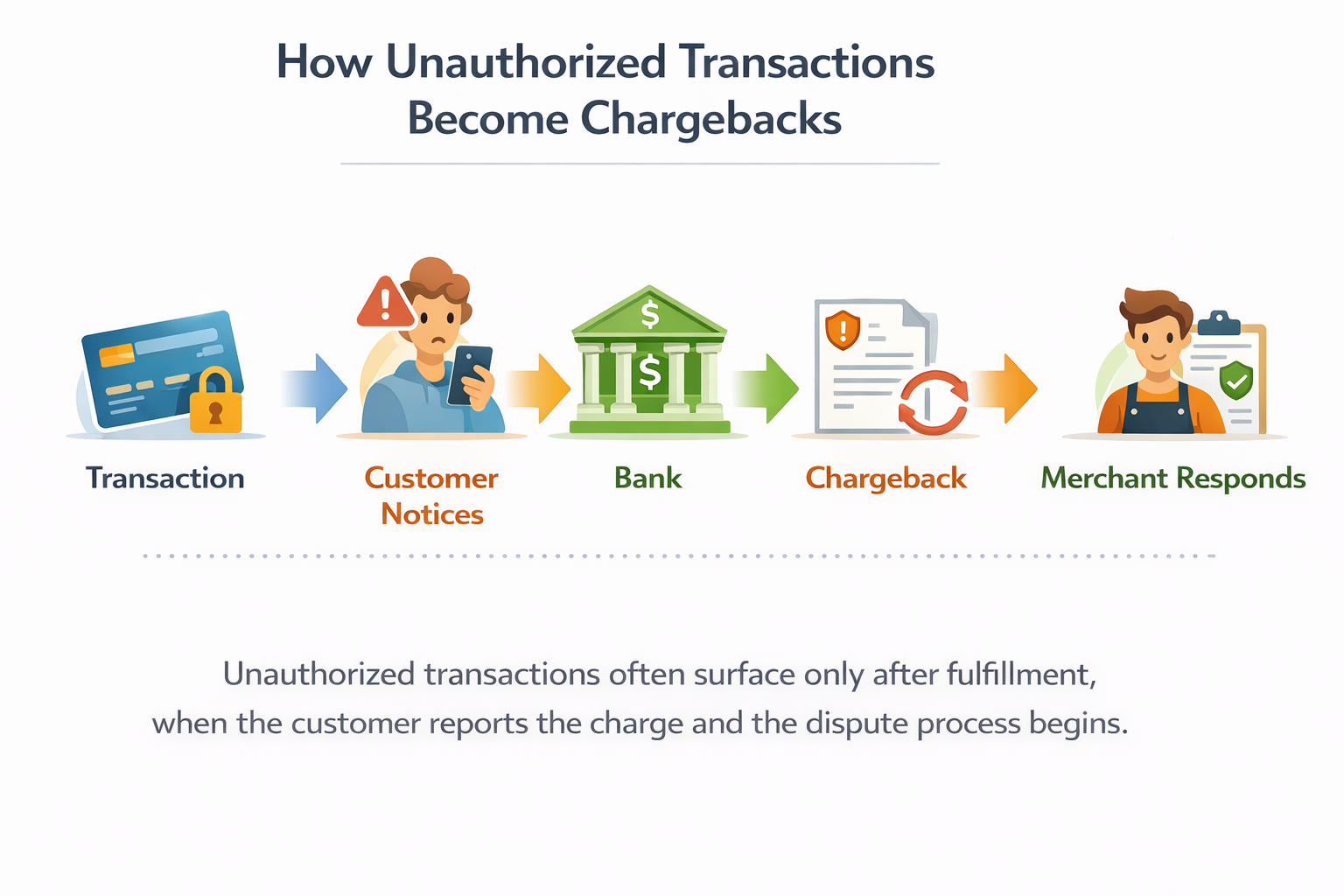
In most cases, the sequence is straightforward. The transaction is completed, the order is fulfilled, and only afterward does the customer flag the charge and file a dispute.
At that point, the transaction enters the chargeback process, and the way it’s evaluated changes.
From the system’s perspective, everything looks valid. The account is real, the payment method is on file, and the transaction was successfully authorized.
From the issuer’s perspective, the situation is simpler: the cardholder denies the charge.
That’s where the gap appears. The system validates the transaction, but the issuer evaluates the outcome.
What looks like a legitimate transaction internally is treated as unauthorized externally. Without clear evidence linking the cardholder to the purchase, these disputes are difficult to resolve with chargeback representment.
For merchants, the outcome is consistent. Merchants lose revenue after fulfillment, the dispute affects chargeback ratios, and they spend time responding to cases with a low probability of recovery.
The failure doesn’t happen at checkout. It happens earlier, when access is granted without enough control.
Preventing unauthorized transactions is more effective than trying to recover them later. Merchants that monitor behavior across the full lifecycle reduce disputes before they happen and avoid losses that can’t be recovered.
Summed Up
Unauthorized transactions don’t fail at checkout. They fail earlier, when access is granted without enough control. The impact shows up later as disputes and chargebacks.
If you’re already dealing with fraud-related disputes, the real question isn’t how they happen. It’s how they’re handled once they turn into losses.
See how Chargeflow helps merchants recover revenue from unauthorized transactions and automate chargeback handling.
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Related ARTICLES
Questions?
we’ve got answers.
Chargeflow collects data from dozens of third party signals, automatically. This allows for much more coverage and much better win rates because the evidence submitted is much more comprehensive and compelling.
Chargeflow collects data like order info, customer messages, and payment details. It builds a full dispute case for you, so you don’t have to lift a finger.
Yes! Chargeflow works with 50+ payment processors. That means one tool for all your chargebacks, no matter how you process payments.
You only pay a percentage of the revenue we help you recover. No upfront fees, no subscriptions — just success-based pricing.
Yes. Chargeflow is SOC 2 Type 2, GDPR, and ISO certified. We use top security standards to keep your data safe.
need more help?
Have a question? We’re here to help. Just hit the chat button to initiate a conversation with support.






















%201.svg)






































.png)


