Card-Present Transaction Fraud: Definition and How to Prevent It
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Card-present fraud costs merchants billions annually, not just in lost transactions, but also in chargebacks, staff time, and inventory issues. From shimming attacks and NFC relay exploits to social engineering at the counter, fraudsters target your culture as much as your technology. Prevention comes down to enforcing chip and contactless as defaults, disabling mag-stripe fallback except by manager override, training staff to recognise behavioural red flags, and using tools like Chargeflow Prevent to block suspicious transactions.
Nothing beats that crisp cha-ching or the happy ding of a successful card tap. It’s the sound of sales closing, inventory turning over, and your business gaining real momentum.
But not every approved transaction delivers the expected win. The same terminal can quietly approve a fraudulent transaction: a stolen card tapped in seconds, a skimmed chip cloned into a counterfeit, or a contactless payment rushed through. It all looks legitimate until the chargeback lands on your dashboard.
This hidden threat is known as card-present transaction fraud. It’s the persistent risk in face-to-face payments. Despite EMV chips and contactless technology reducing counterfeit fraud by up to 87% in mature markets, fraudsters adapt. Lost or stolen cards, shimming attacks, and low-value tap exploits...Card-present fraud accounts for $6–10 billion in annual losses.
This article examines everything you must know about card-present fraud. We’ll take you behind the counter to show you precisely how these heists work today and how to ensure your next approved transaction stays in your bank account.
What Is Card-Present (CP) Fraud?
Card-present (CP) fraud is unauthorized in-person payment fraud where a criminal physically uses a stolen, counterfeit, or cloned credential (EMV card, mag-stripe fallback, or NFC digital wallet tap) to complete a fraudulent purchase at your POS terminal that appears legitimate in real time.
This is often referred to as a “proximity attack” because the fraud requires close physical access to the terminal. Here are the key characteristics of card-present fraud:
- The card (or token in a digital wallet) is “presented” in person through a swipe, insert (chip), tap (contactless/NFC), or even manual key entry in rare cases.
- Approval occurs in real-time, often accompanied by a beep or ding, making the transaction appear legitimate.
- Chargebacks typically surface weeks later, after the criminal is long gone with the goods or services.
CP fraud differs from broader card fraud (especially remote card-not-present fraud) in its physical, in-person nature.
How Card-Present Transactions Work
A standard CP transaction follows these steps:
- A customer presents payment at checkout by inserting a chip card, tapping a contactless card/phone/watch, swiping a magnetic stripe, or handing over a card for manual entry.
- The POS terminal reads data.
- For chip/contactless: Encrypted dynamic data (one-time code) is generated.
- For swipe (rare now due to tech advances): The system reads magnetic stripe data.
- The terminal sends the payment authorization request with details to your acquirer/processor, who forwards the details to the card network (Visa, Mastercard, Amex, or Discover) and then to the card issuer or bank.
- The issuer approves or declines after checking funds, fraud rules, and (for chip) validating the cryptogram, with the response returning in seconds.
- The transaction is completed with a receipt printed, goods handed over, and funds settling later (ideally 1-3 days).
Card-present transaction fraud exploits the need for optimal speed and seamless checkout in in-person transactions.
Fraudsters use lost or stolen cards and no-PIN contactless taps that can be completed in seconds with almost no immediate risk. Merchants struggle with the convenience-versus-security trade-off. Any extra verification that could stop these attacks would slow down every legitimate customer and hurt the fast, frictionless experience that drives in-store sales.

Common Types of Card-Present Transaction Fraud
Fraudsters have largely abandoned full card cloning. EMV’s dynamic codes make it extremely difficult and rarely worth the effort anymore. Instead, they prefer low-effort, high-speed opportunism that preys on the very fabrics of a truly effortless checkout. Scaling brands are increasingly targeted by technical bypasses and social engineering designed to trick both the terminal and the human behind the counter. Here are the most common card-present fraud patterns worth noting:
1) Shimming and Fallback Attacks
While skimmers (which read magnetic stripes) are nearly extinct in modern retail, Shimmers are the new frontier.
A shim is a paper-thin, microscopic device inserted into your terminal’s chip slot. It doesn’t steal the magnetic stripe. It intercepts the communication between your POS and the EMV chip.
The goal? To trigger a technical error. When the chip fails to read because of the shimmer, the criminal waits for your staff to say, “The chip isn’t working, let’s try swiping it.” The moment that card is swiped, the liability shift flips, and you, the merchant, becomes 100% responsible for the fraudulent transaction.
2) NFC Relay and Ghost Tapping
This is, perhaps, the most sophisticated threat facing high-traffic showrooms and pop-up events.
Using tools like NFCGate, a fraudster relays a signal from a legitimate card located elsewhere (e.g., in the pocket of someone in a nearby coffee shop) to a phone at your register.
The scammer then taps their phone (Apple/Google Pay), and the transaction is approved. To your system, it looks like a high-security mobile wallet tap. In reality, the person standing in front of you doesn’t own the credentials. They are essentially mules beaming someone else’s card into your store.
3) Forced Manual Entry
This is the low-tech version of card-present fraud. But don’t be carried away by the mundane nature; it still costs scaling brands millions. It exploits human kindness and speed.
For social engineering CP frauds, the scammer presents a card they have intentionally damaged (scratched chip). They may even play the “damsel in distress” role, claiming they are in a rush or that this happens “all the time.”
They convince your employee to manually key in the 16-digit card number and CVV on the terminal. The moment they do this, it’s game over! Manually keyed transactions are processed as card-not-present (CNP) on a physical device, stripping away almost all your legal defenses during a dispute.
4) First-Party Misuse
For many Chargeflow clients, the biggest threat is their own customer.
First-party misuse happens in card-present transactions. The customer visits your store, buys a high-value item, and then turns around two weeks later to dispute the transaction. Because the customer was physically in-store, they assume your evidence, often just a thermal receipt or signature, won’t suffice in proving legitimate authorization.
In these cases, your strongest defense isn’t the receipt. It’s the data: EMV authentication records, POS logs, device verification, SKU-level proof of delivery, and any digital-physical linkage that ties the transaction to the cardholder.
Card-Present vs. Card-Not-Present Fraud: Key Differences
For many brands, the line between ‘online’ and ‘in-store’ is blurring due to the rise of Unified Commerce. Inventory, payment data, and customer identities are integrated into a single ecosystem to support hybrid behaviors, such as Buy Online, Pick In-store (BOPIS) and showrooming.
But payment networks still classify transactions by channel. Card-present and card-not-present transactions operate under different risk models, liability rules, and dispute frameworks.
While merchants see one customer journey, the networks see two distinct risk environments.
Understanding the structural divide and how CP and CNP fraud are treated is vital for merchants operating across channels.
The Fundamental Variance
At the most basic level, the distinction between CN fraud and CNP fraud is proof of presence.
- In CNP fraud environments, the proof of transaction legitimacy is a collection of digital signals. These include IP address, CVV, 3DS, etc.
- In CP, the proof is a physical cryptographic handshake between an EMV chip and your hardware.
The Liability Shift
The single most important concept for modern payment collection is who pays when things go wrong. The “Liability Shift” is a rule set by the card networks that determines which party is financially responsible for a fraudulent transaction.
- In the CP world, if you have an EMV-compliant terminal and a customer “dips” a stolen chip card, the bank or card issuer absorbs the loss. The exception to this rule is if you allow a “Fullback Swipe” (sliding the magnetic stripe because the chip failed) or a manual entry was used. You effectively waive your protection.
- In CNP contexts, you, the merchant, are liable for online fraud by default. The exception is if you implement 3DS or use certain digital wallet protocols.
How Card-Present Fraud Happens at the Point of Sale
Here’s what most merchants miss: the $8,000 fraudulent transaction that lands on your account didn’t start at the register. It started with your training materials.
Every time you tell your staff to “create a frictionless experience” or “never let technical difficulties stand in the way of a sale,” you’re teaching them to bypass the security measures designed to protect you. You’re inadvertently training them to ignore red flags.
Fraudsters understand this better than most business owners. They don’t dress like criminals or act suspiciously. They present themselves as your ideal customer, so you don’t suspect a thing.
Warning Signs of Card-Present Fraud for Merchants
Behavioral Red Flags
Train your staff to notice when standard checkout procedures are being bypassed or rushed. These are the most common card-present transaction fraud behavioral red flags:
- Urgency to bypass verification: Insisting on a swipe or manual entry immediately after a chip failure.
- Rapid small-value purchases: Multiple contactless taps under verification thresholds, often across several locations.
- Immediate pivot after a decline: Switching cards, requesting manual entry, or using gift cards instead of following normal decline protocols.
- Attempts to control the checkout flow: Creating distractions, rushing the process, or discouraging verification.
Physical Card Indicators
Sometimes the risk is embedded in the card itself. These are the most common physical card indicators of card-present transaction fraud:
- Scratched or damaged chip area that seems intentional.
- Cards that appear old or worn despite being “newly issued.”
- Requests to bypass chip insertion and swipe instead.
- Signs of tampering or mismatched signatures.
- The customer presents a premium, heavy-metal card. But when chipped or tapped, your POS screen shows “DEBIT” or “PREPAID” instead of “CREDIT.”
Remember, card-present transaction fraud seeks to exploit your culture, not necessarily your technology. That’s why it mostly succeeds. When your team operates under the belief that friction equals poor service, fraudsters weaponize that assumption. They know you’ve trained your staff to find workarounds when chips fail or systems lag.
The Business Impact of Card-Present Fraud
There’s a reason most merchants don’t worry much about card-present transaction fraud. The customer is standing right there with a physical card. What could go wrong?
Turns out, a lot. The damages extend far beyond the transaction itself.
Just like CNP fraud, card-present fraud doesn’t cost you the transaction value. It costs you:
- The product that walked out
- A chargeback fee when the card owner claws the money back
- 8-12 hours of staff time investigating and disputing the chargeback
- The margin on legitimate sales you need to recover the loss
But that’s not all.
Ancillary costs include:
- Operational disruption, as staff second-guessing transactions increases checkout time, frustrates legitimate customers, and hurts morale.
- Inventory consequences: systems show revenue that never reached your balance sheet, reorder triggers fire based on phantom demand, and overall demand forecasting becomes less reliable.
- Brand damage as a result of inefficiencies of added fraud detection tools at checkout.
- Strategic and financial constraints when processors begin strengthening leverage through higher reserves, stricter rules, and delayed settlement.
When you do the math, you’ll quickly realize why every $1 fraud costs you at least $4.61.
Challenges in Detecting and Preventing CP Fraud
Spotting and stopping CP fraud at the POS can be a headache for merchants. The core problem is that you’re trying to secure transactions that are built to happen lightning fast.
As indicated earlier, it’s a classic Cash-22. Any extra stop risks killing the customer experience you work hard to deliver. But add too few controls? Fraudsters exploit gaps.
Here are four of the biggest roadblocks in detecting and preventing CP fraud:
The Speed-Security Tug-of-War
Transaction approvals are supposed to happen in seconds. That’s the point of modern payments. And so, inserting meaningful checks, such as requesting ID or velocity flags, can create lines, annoy customers, and impact conversions.
Fraudsters Keep Evolving
While card cloning is no longer as rampant as it used to be, thanks to EMV, lost or stolen cards are still a thing. A Forbes article reported that at least 14 million credit cards were stolen last year, with 1 million card numbers given away for free on the dark web.
Card-present transaction frauds, such as shimming and no-PIN contactless exploits under limits, persist because they’re quick and low-risk. A thief taps before the owner reports it.
Staff Turnover Kills Consistency
Retail has high churn. New hires often miss subtle fraud signs because training gets squeezed. One bad shift can open doors to excessive CP fraud.
Fraudsters look for these gaps. They hit during rushes. They target new employees and understaffed locations. They’re timing your security.
The Insider Threat You Can’t Tech Your Way Out of
Some card-present fraud doesn’t come from outside. Employees process fake returns. They keep customer card details, disable security prompts, or help suspicious transactions go through.
Because these transactions are processed by authorized users, they look completely legitimate to your system. You can monitor for anomalies, but that’s not enough to eliminate the problem. You need fundamental trust to run a retail operation.
Now that you know how card-present fraud unfolds at the point of sale, the question is: How do you put practical, low-friction defenses in place to protect your revenue without turning every customer interaction into a security checkpoint? Let’s examine that:
Card-Present Fraud Prevention Best Practices
The good news today is that combining simple tech tweaks, staff habits, and smart policies can help you stop most card-present transaction fraud. And you can do that while keeping checkout fast and customers happy.
Here’s a proven, merchant-first playbook that focuses on high-impact actions with minimal disruption:
1) Push Chip and Contactless as the Default
Gently guide customers toward inserting the chip or tapping NFC instead of swiping. Where and if the terminal allows, disable or discourage mag-stripe fallback. Why? It’s slower, less secure, and often triggers liability shifts under EMV rules.
Contactless is faster for your lines, anyway. It also uses tokenization and dynamic codes, making data theft far more challenging.
2) Build Consistent Staff Training Routines
Run short, regular sessions focused on real CP fraud signs. Ensure everyone knows the difference between a customer who is genuinely having a bad day and a fraudster trying to manipulate their way through the process.
Furthermore, teach polite ways to request photo ID on higher-value or risky transactions, and make daily terminal inspections part of opening/closing routines, if applicable. This helps you uncover shims/skimmers on readers/slots.
High-turnover retail teams thrive when training is quick, visual, and repeated.
3) Harden Your POS Hardware
Use tamper-evident terminals that alert when opened or compromised. Disable mag stripe fallback except for manual manager override. Forcing the swipe through the same terminal that rejected the chip is the most common fraud technique, and legitimately damaged chips are rare enough to be handled as exceptions.
Most importantly, force PIN entry above your contactless limit. If your region allows $100 tap-to-pay, and you’ve noticed CP fraudsters exploiting this, set your threshold at $50. This inconvenience of entering a PIN is minor compared to the cost of not requiring one.
4) Enhance Customer Verification and Red-Flag Monitoring
For suspicious or high-value transactions, require full authorization on every transaction. Consider deploying Code 10 calls. If something feels off, quietly call the processor/issuer for a “Code 10” authorization request. This alerts the issuer discreetly without tipping off the customers.
Check for card matching and watch for patterns, such as multiple attempts, large purchases of fraud-prone items, or forcing fallback methods.
5) Implement Emerging Defenses Where Feasible
In hybrid setups (e.g., BOPIS), integrate with CNP tools like Chargeflow Prevent, if applicable, and derisk the transaction before in-store fulfillment.
This structured approach keeps losses down without sacrificing sales velocity. In the next section, we’ll cover how to respond when something does slip through.

How Merchants Should Respond to Card-Present Fraud Incidents
When a transaction feels off, the goal should be to move the transaction back into a safe harbor or terminate it without a scene. Here’s the modern 3-phase protocol for scaling brands:
Phase 1: Immediate Response
The moment a red flag appears, your staff should switch to “system-blame.”
The script: “I’m so sorry, the terminal is giving me a security handshake error. Our system won’t let me bypass this for a transaction of this size.”
Why this works: It removes the personal element that scammers manipulate. The staff member isn’t accusing the customer. The mean machine is just doing its job. And guess what, this prevents the aggressive distraction tactic fraudsters use to pressure staff.
Next Steps:
- Discreetly initiate a Code 10 authorization.
- Politely request photo ID if policy allows (compare name/photo/signature subtly).
- If red flags escalate or the customer becomes aggressive, prioritize de-escalation. Involve a manager/security, decline politely (“This didn’t go through, perhaps try another card?”). But never override a decline.
Phase 2: Terminal Pivot
If you suspect a device-level attack (like a Relay Attack or Shimming), don’t just keep trying on the same register. Politely ask the customer to move to a different register: “Let’s try this terminal. Register 1 has been acting up with NFC taps all morning.”
Why this is vital: If the lag or error disappears on Register 2, you likely have a hardware compromise on Register 1. If the error persists, the problem is the credential, not the hardware.
Phase 3: Post-Incident Safeguard and Recovery
In cases where a suspicious transaction was approved, perhaps because the fraudster successfully social-engineered a fallback, you need safeguards. Immediately flag the transaction. Most modern systems allow for internal notes.
Immediate Actions:
- Flag the transaction ID in your POS system with internal notes: e.g., Customer claimed business card chip was damaged; insisted on manual key-in. Staff observed rushed behavior and forced fallback.
- Capture exact timestamp or approval beep, with staff notes on observations.
- Pull and document a 15-30 second video clip from the in-store camera (if available and legal) showing interaction and card presentation.
- Inspect the terminal for tampering (wiggle test, check for overlays or cameras) and report to the processor.
This allows you to pull a 15-second video clip later when the chargeback lands. If none of these are applicable, and the chargeback is the only rude awakening to the card fraud, that’s where Chargeflow comes in. Chargeflow helps merchants recover chargebacks on autopilot. And you only pay upon success.
If you have an online component, adding Chargeflow is non-negotiable. It turns potential card-present transaction incidents into recoverable disputes, often with 4x better recovery rates.
Card-Present Fraud Trends and Emerging Threats
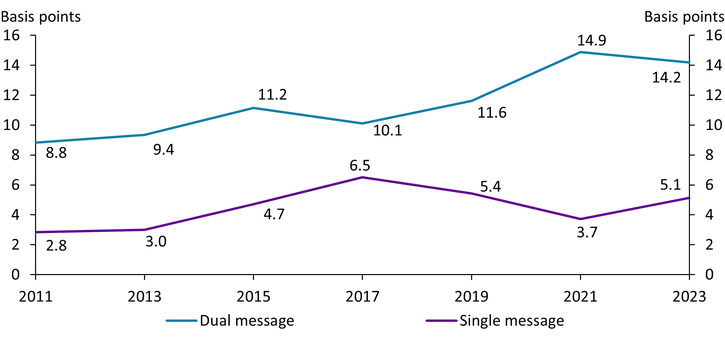
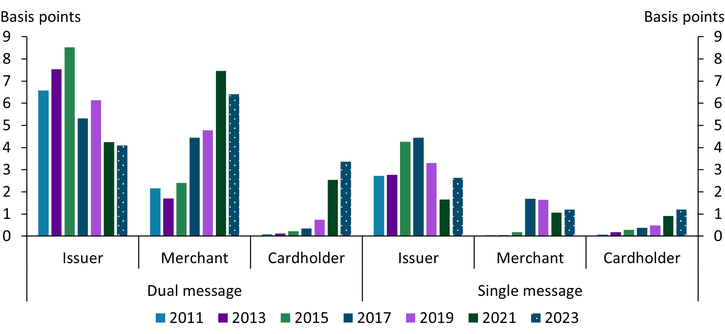
The fraud landscape is becoming more active by the day. According to the Kansas City Payments Research Systems Briefing, “the U.S. payments industry migrated to EMV chip-card technology in 2015 to mitigate card-present fraud. Since then, however, payment card fraud has continued to climb.”
U.S. CP rates remain higher than in regions like Australia (1.0 basis points) or the EEA (0.7 basis points), partly due to slower full EMV/contactless adoption in some segments.
Below are some emerging threats worth noting:
NFC Relay Attacks
The threat is rare, but real. A fraudster can use specialized equipment to relay an NFC signal from a victim's phone to your terminal. The transaction appears completely legitimate. The encrypted mobile wallet passes all security checks without issues.
Why it Matters: When the real cardholder disputes the charge, you have no physical evidence of who tapped at your register. The technical sophistication required keeps this relatively uncommon.
What to watch for: Contactless transactions that process unusually slowly (2-5 seconds lag) or customers who seem disconnected from their payment device.
BORIS Fraud: The Gift Card Version
Buy Online, Return In-Store has evolved. Fraudsters now specifically target gift card returns because they’re untraceable and easily converted to cash on secondary markets.
The pattern: The criminal buys high-value items online with a stolen card, chooses in-store pickup, then immediately drives to a different location to return the items. The scammer claims they lost the receipt and pressures staff to issue a generic gift card instead of a refund to the original payment method.
The damage: You eat the chargeback on the original purchase, lose the inventory, and hand over a gift card that gets sold for crypto within hours.
What prevents this: Pair policy upgrade with Chargeflow Prevent so that AI can screen out such scammers from your system. Train your staff to escalate any return without proof of original payment.
Bluetooth-Enabled Skimming Devices
Modern skimmers are smaller, smarter, and harder to detect. They sit inside your chip reader and transmit stolen data wirelessly; no need for the criminal to return and physically retrieve anything.
You may not know until you see a cluster of counterfeit fraud chargebacks from cards that were used at a specific terminal. By then, dozens of customers have been compromised.
As we indicated earlier, regular physical inspection of terminals helps prevent this. Act quickly to investigate underlying causes as soon as you notice multiple fraud reports associated with the same terminal.
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Related ARTICLES
Questions?
we’ve got answers.
Chargeflow collects data from dozens of third party signals, automatically. This allows for much more coverage and much better win rates because the evidence submitted is much more comprehensive and compelling.
Chargeflow collects data like order info, customer messages, and payment details. It builds a full dispute case for you, so you don’t have to lift a finger.
Yes! Chargeflow works with 50+ payment processors. That means one tool for all your chargebacks, no matter how you process payments.
You only pay a percentage of the revenue we help you recover. No upfront fees, no subscriptions — just success-based pricing.
Yes. Chargeflow is SOC 2 Type 2, GDPR, and ISO certified. We use top security standards to keep your data safe.
need more help?
Have a question? We’re here to help. Just hit the chat button to initiate a conversation with support.






















%201.svg)






































.png)