Card-Not-Present Fraud: What It Is and How to Prevent It
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Card-Not-Present (CNP) fraud dominates modern payments. It causes 73% or $12.5B annual U.S. card fraud losses. Today’s CNP fraud leverages automated attacks, mass credentialling, account takeover, synthetic identities, and triangulation. Merchants bear the liability and operational cost. Gateways and banks detect broad attacks and card-level anomalies. Effective merchant defenses require pre-screening high-risk orders, layered authentication, network tokenization, merchant-side intelligence, and automated evidence with tools like Chargeflow automation.
Card-Not-Present (CNP) fraud isn’t necessarily a new phenomenon. It’s just gotten a massive digital upgrade. While the first “remote” fraud occurred in 1899 through a stolen train ticket, the evolution of the threat has been relentless:
- 1970s: Thieves raided mailboxes for mail-order catalogs and carbon copy receipts.
- 1990s: “AOHell” pioneered phishing, tricking early internet users into handing over card details.
- 2015: The EMV chip technology made physical cards harder to clone, causing fraudsters to move almost entirely to online checkout lanes.
The current reality is that CNP fraud losses were estimated to have reached $12.5 billion in the U.S. alone, accounting for nearly 73% of all card fraud. It is no longer a question of if a merchant will suffer CNP fraud losses, but how they will defend themselves.
This guide breaks down the mechanics of modern card-not-present fraud and the specific protocols you can implement to stop it.
What Is Card-Not-Present (CNP) Fraud?
In its simplest terms, Card-Not-Present (CNP) fraud is the unauthorized use of payment credentials in any environment where the physical card cannot be verified by the merchant.
For a fraud analyst or merchant, however, the CNP definition would be more precise: It is an authentication exploit. CNP fraud occurs when an attacker uses a set of stolen, static data points, the Primary Account Number (PIN), CVV2, and Expiry, to successfully mimic a legitimate cardholder within a digital, mobile, or telephonic channel.
Because the merchant cannot see the card or the customer, the entire security of the transaction rests on the assumption that possession of the data equals authorization by the owner. CNP fraud is the systemic proof that this assumption is false.
Card-Present vs. Card-Not-Present Fraud: Key Differences
Both card-present fraud and card-not-present fraud involve unauthorised use of payment credentials. The real difference is how fraudsters execute the attack, how difficult it is to scale, and how payment networks allocate fraud liability.
Here are the key considerations:
1) Execution: Physical Access vs Remote Exploitation
CP fraud generally requires physical or proximity-based interaction with the payment infrastructure. Under global EMVCo standards, a chip-enabled transaction requires a localized, dynamic cryptographic interaction between the card (or a provisioned mobile wallet) and the terminal.
In contrast, CNP fraud requires no such proximity and hardware-level handshake. The attacker only needs to provide fixed data sets. Merchants are merely validating a string of characters.
- The proof-of-life requirement in CNP transactions means that even if a fraudster intercepts the data from a transaction, that data is mathematically useless for any future purchase. The attacker must physically possess the card, compromise a digital wallet, or use specialized hardware to relay an NFC signal. This creates a high friction that prevents the attack from being launched globally from a single terminal.
- In card-not-present fraud, because these credentials are static, they are highly susceptible to exfiltration. Database breaches, phishing, or form jacking (Magecart) can compromise data points. Once harvested, they are sold on dark web marketplaces to be used across thousands of merchants simultaneously.
2) Scalability: Localized Fraud vs. Automated Attacks
To scale a card-present fraud operation, perps must manage a decentralized network of human operators. These actors must physically visit retail locations, handle counterfeit plastic, and risk face-to-face interaction with staff or surveillance.
Even with sophisticated operations, the attack is limited by geography and human speed. The risk-to-reward ratio is dampened by the logistical overhead of the physical world.
In card-not-present fraud environments, automated orchestration replaces the human vector. A single digital API or web form can test thousands of stolen sets across hundreds of different merchant gateways at once.
3) Risk Distribution: Merchant Protection vs Merchant Exposure
The last, and most critical, distinction between card-present fraud and card-not-present fraud is the liability framework.
The card network’s liability created a safe harbor, where a card issuer bears the loss of counterfeit fraud if a merchant processed a card-present transaction with the right hardware.
In the CNP world, that safety net is absent, unless you are specifically using 3DS correctly. This moves the burden of proof back to the bank.
With all that said, let’s examine how CNP fraud pans out.
How Card-Not-Present Fraud Works
According to Mastercard, fraud that targets payments is growing more complex and sophisticated. The criminal use of AI and the increasing standardization and reproduction of malware and other technologies: They act like a digital equivalent of an old-fashioned burglary tool.
For the professional fraud analyst, this transformation means viewing CNP exploitation as a disciplined, three-phase industrial cycle: acquisition, refinement, and monetization.
Here’s how CNP fraud plays out:
Mass Credential Acquisition
Stolen data now saturates the market. In 2024, the “Mother of All Breaches” (MOAB) highlighted that fraudsters treat private records as a cheap, abundant commodity.
Professionals categorize acquisition into three primary vectors:
- Systemic Breaches: These are high-yield database compromises that flood dark-web markets with millions of Fullz or complete credential sets simultaneously.
- Active Harvesting (Magecart/eSkimming): A sophisticated middleman attack where malicious JavaScript is injected into eCommerce checkout pages. This captures at the point of entry, often bypassing standard encryption protocols.
- Algorithmic Generation (BIN Attacks): Also known as Issuer Enumeration, it bypasses the need for a breach entirely. Here, the attacker can use a known Bank Identification Number and brute-force algorithms to guess valid PAN, Expiry, and CVV combinations.
Automated Validation or Refining Process
Raw data is only useful when verified. Attackers use carding to distinguish static cards from live ones, effectively weaponizing your infrastructure.
Card testing takes different forms, but the ultimate goal is an approved response, which instantly triples the resale value of a raw credential.
Exploitation and Liquidation
Once a card is hot, the card-not-present lifecycle moves toward exit. The objective is to convert the digital credential into liquid value before the issuer’s fraud detection system (FDS) flags the pattern.
Fraudsters increasingly leverage Peer-to-Peer services to wash funds and transfer balances through a chain of compromised accounts that hide the paper trail before the inevitable chargeback arrives.
“One alarming fraud trend in 2025 is the increasing industrialization of support services and technology that allows fraudsters to maximize their effectiveness."
"One such popular tool allows scam operators to rewrite the code on an online retailer’s payment page and then steal, or 'skim,' payment information as transactions happen."
"There were 10,500 such hacks active in 2025, leading to the compromise of over 23 million online transactions.” – Top Payment Fraud Risks and Strategic Implications for 2026 by Recorded Future
Common Types of Card-Not-Present Fraud
Card-not-present fraud typologies are professionally categorized by the source of the actor: external criminal syndicates, automated bot networks, or the customers themselves.
First-Party Fraud
Now recognized by most merchants as the primary threat to eCommerce margins, friendly fraud has evolved from a nuisance into a systemic crisis.
Mastercard attributes 70% of all credit card fraud to friendly fraud, with merchants absorbing over 132 billion in annual losses. By the end of 2026, global chargeback volumes are projected to reach 337 million transactions, a 42% spike from 2023 levels.
Chargeback fraud has proliferated because the customer, not a third party, perpetrated the act. And so, unlike traditional fraud, the transaction data (IP, device fingerprint, CVV) is mostly 100% legitimate, rendering most legacy front-end filters useless.
Automated Infrastructure Attacks
As highlighted earlier, BIN and enumeration attacks are not targeted thefts but rather brute-force exploitation of the payment gateway.
The U.S remains the primary target, accounting for 58% of global issuer enumeration attacks. These attacks don't just result in fraud; the high volume of declines can damage a merchant’s reputation with processors and trigger penalties.
Account Takeover (ATO) Fraud
ATO fraud is evolving beyond simple credential theft. While historically driven by password guessing and credential stuffing, modern ATO increasingly exploits stolen browser sessions to bypass authentication controls entirely.
Using infostealer malware, attackers harvest browser cookies and session tokens from compromised devices. This allows them to replay an already authenticated session (a “pass-the-cookie” attack) and appear as a legitimate logged-in user. Because the authentication step has already been completed, these attacks can bypass MFA challenges tied only to the login process.
Once inside a trusted account, attackers typically monetize the access quickly. Stored payment methods, loyalty balances, and established transaction records enable high-value transactions less likely to trigger risk controls.
Synthetic Identity Fraud
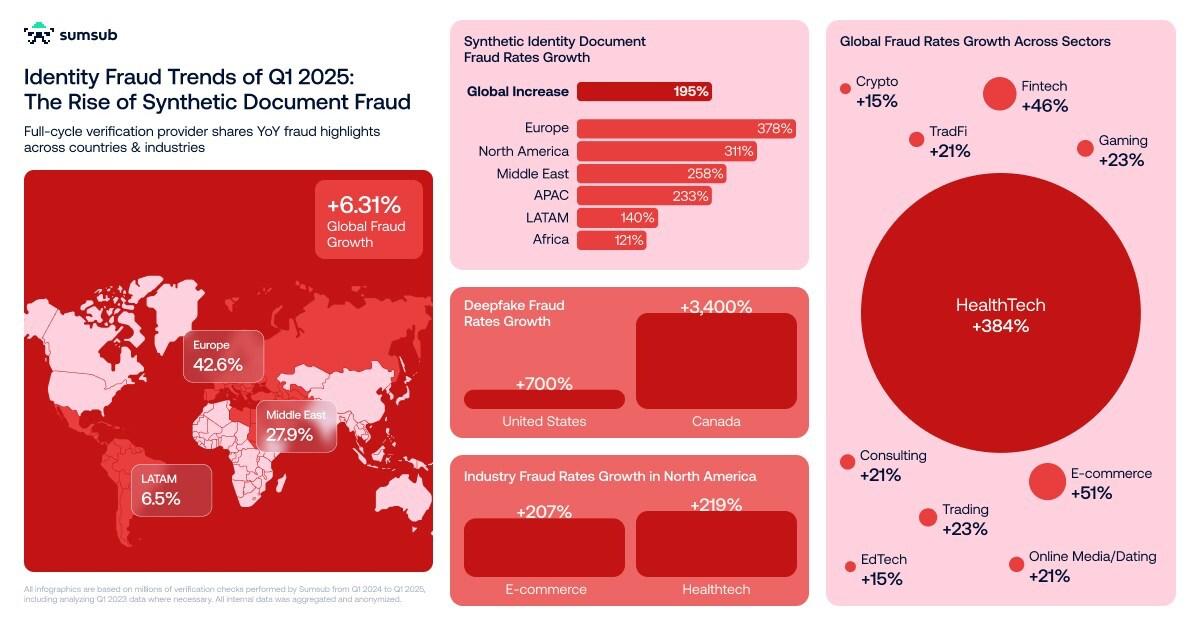
Synthetic identity fraud has evolved beyond simple data mixing. Fraudsters now combine stolen personal identity information with AI-generated attributes to build phantom personas that have zero real-world history and are therefore invisible to traditional verification systems.
Generative AI has accelerated this shift dramatically. Synthetic identity document fraud surged 300% in North America between Q1 2024 and Q1 2025. Attackers now routinely produce hyper-realistic live selfies, utility bills, forged documents, and consistent digital footprints that clear standard automated KYC checks at scale.
This is a mature, high-ROI criminal business model. Unlike classic CNP fraud, which is built for immediate liquidation, synthetic identities are methodically nurtured.
Triangulation Fraud
Triangulation fraud is a nested card-not-present fraud scheme that turns legitimate consumers into unwitting accomplices.
The fraudster sets up a shadow storefront, often on eBay, Facebook Marketplace, or a convincing independent site, offering popular items at steep discounts. When a real customer buys and pays the fraudster, the attacker immediately uses stolen card details to purchase the same product from a legitimate merchant and ships it to the buyer’s address.
The actual customer receives the goods and is satisfied, so they never dispute anything. Weeks or, probably months, later, the legitimate cardholder spots the unauthorized charge and files a chargeback. The merchant loses both the inventory and the revenue, absorbs the fees, and has virtually zero recourse. Proof of delivery exists to a real address. Meanwhile, the fraudster pockets clean profit from the shadow sale with almost zero traceability.
How Card-Not-Present Fraud Affects Businesses and Customers
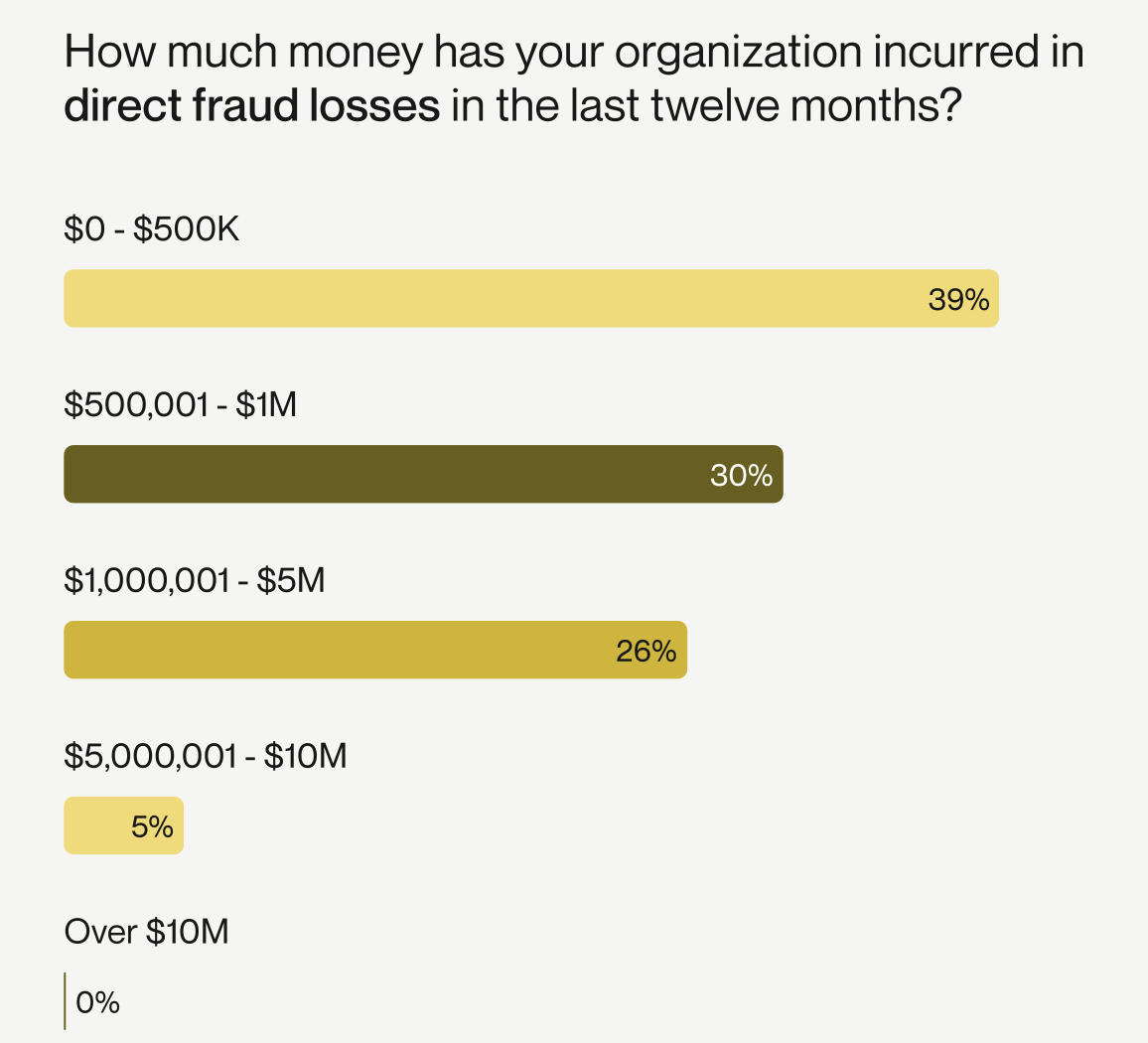
Merchants absorb the default financial and operational burden of card-not-present fraud because liability starts with them. It quietly erodes customer lifetime value and forces constant mediation spending you’d otherwise never have to make.
Customers face personal disruption that often translates into permanent trust loss and churn.
Card-Not-Present Fraud Impact on Merchants
Without tools like Chargeflow Prevent and 3DS controls, merchants are the insurer of record. They eat the full fraud amount and every downstream cost.
Industry estimates put the U.S. merchant multiplier at nearly 5x for every dollar of fraud. This shows up operationally as:
- Complete exposure on almost every fraudulent order unless liability is actively shifted.
- Heavy dispute volumes that tie up risk and finance teams, unless fraudulent transactions are blocked before fulfilment.
- Higher processor fees, reserve requirements, and strained acquiring bank relationships due to high chargeback rates.
- Quiet erosion of margins and growth from churned customers who never return, and actively campaign against your brand.
Card-Not-Present Fraud Impact on Customers
CNP fraud leads to legitimate cardholders receiving unauthorized charges, frozen accounts during investigations, hours on the phone with issuers, and, in serious cases, broader identity compromise.
Customers often channel their frustration to merchants. Many victims blame the merchant where the transaction appeared, then simply stop shopping there. The issuer may reverse the charge, but the relationship with your brand is usually dead.
Warning Signs of Card-Not-Present Fraud Attacks
Card-not-present fraud emerges through a cluster of subtle, interconnected signals. The highest-performing fraud teams, those that consistently maintain chargeback ratios below well below Visa's 0.65% monitoring threshold, spot these patterns in real-time and intervene before the attack scales.
Here are key signals to watch:
Telemetry and Environment Spoofing
Sophisticated fraud operations now leverage residential proxy networks and environment spoofing tools. Developers can now provide a user-agent, and libraries take care of updating the TLS fingerprint accordingly, which particularly helps attackers bypass server-side-only detection mechanisms.
Watch for mismatches between browser/device fingerprints and underlying network telemetry. A user-agent claiming macOS Safari while TCP/IP headers indicate a Linux or virtualized environment is a key red flag.
Behavioral Biometrics Deviations
Look for anomalies in hesitation patterns, correction behavior, and the temporal distribution of user actions.
While automation has become increasingly sophisticated at mimicking human behavior, measurable deviations remain. If an account user is known for being a quick and accurate typer, the system could flag a session if it detects that the current user is much slower. Keystroke dynamics can identify bots whose typing patterns may be too even or too rapid when compared to human users.
Modern fraud tools attempt to mask these patterns. For instance, Ghost cursor can help bots generate more realistic and human-like mouse movements using Bezier curves instead of moving the mouse in a straight line. But statistical analysis of interaction timing, navigation sequences, and form completion patterns can still differentiate automated sessions from genuine user behavior.
Low-Velocity Drip Attacks
Classic velocity spikes are now easier to spot. The newer threat is the low-and-slow heartbeat pattern, where steady small authorizations spread across hours or days from rotating IPs to stay under the radar. Clusters of probe transactions or Account Name Inquiry activity often precede larger coordinated purchases.
Post-Purchase Shipping Manipulation
Many high-value CNP fraud attacks involve legitimate-looking orders followed by quick intervention. Look for rapid address changes, rerouting requests, “hold for pickup” instructions, or shipments directed to known reshipper addresses and freight-forwarder hubs.
Multiple orders converging on the same non-residential delivery points should trigger immediate scrutiny.
When two of these signals align on the same session or customer profile, elevated scrutiny is warranted. The most effective response combines automated step-up authentication with a tool like Prevent for medium-risk signals with manual review for high-confidence pattern matches.
Again, top fraud teams no longer evaluate transactions in isolation. They look for infrastructure convergence patterns. Multiple seemingly unrelated transactions sharing common technical elements may indicate a coordinated operation even when traditional fraud signals appear clean.
Challenges in Card-Not-Present Fraud Prevention and Detection
Preventing card-not-present fraud is inherently asymmetrical. For a fraudster, the hardest part is writing the code or buying stolen data. After that, scaling requires marginal cost. But for merchants, every defensive decision has a real-world cost.
Effective fraud management requires balancing the need for controlled risk with revenue and trust preservation.
Here are the key structural hurdles:
The Friction-to-Revenue Tradeoff
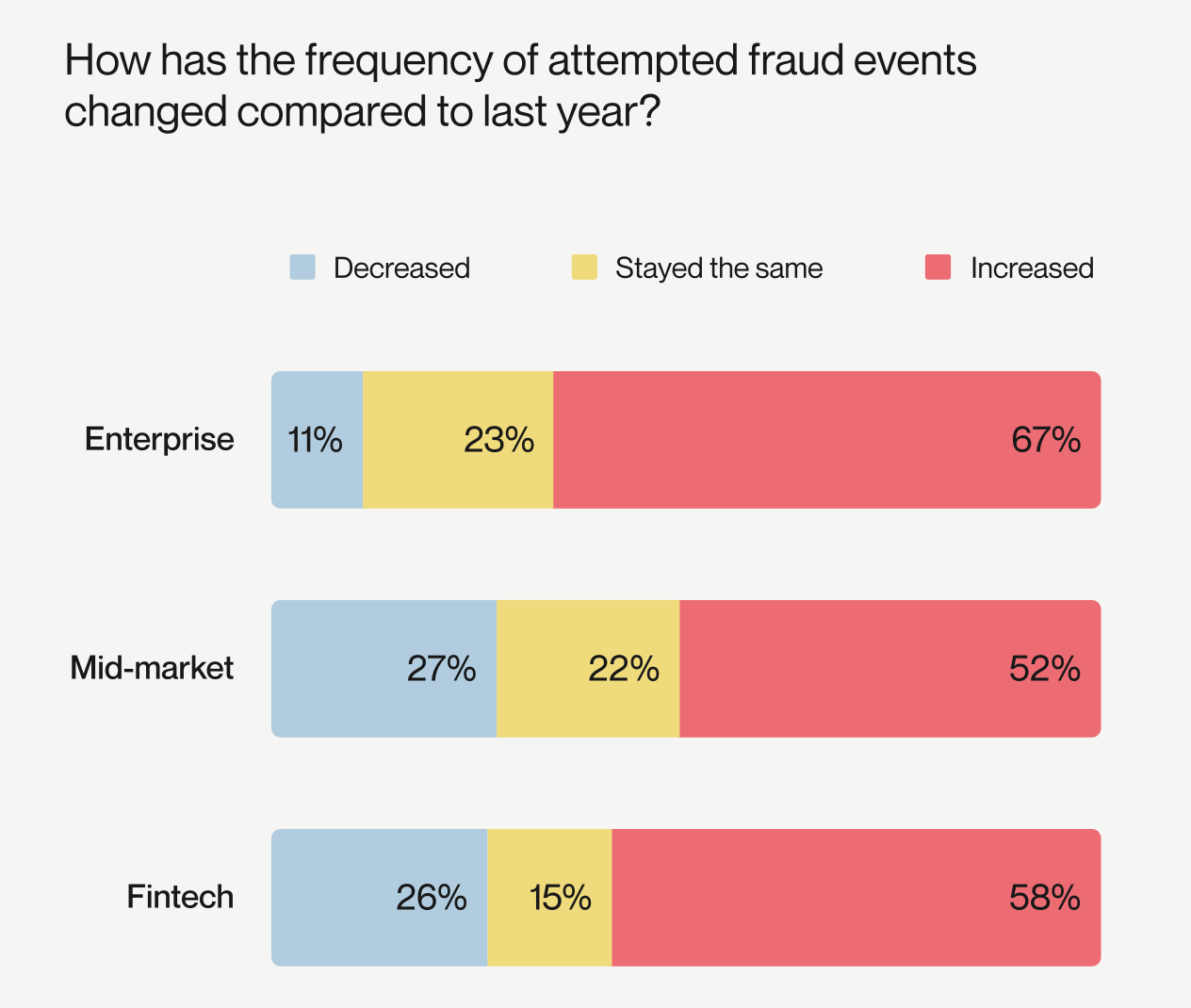
Aggressive rules catch fraud but spike false declines. This hurts conversion and inflates customer acquisition costs. Static blocks often flag legitimate buyers. For instance, 2025 Alloy’s State of Fraud Report found that fraud controls drove churn at 59% of organizations last year.
Merchants now favor risk-based approaches that apply friction where it matters and approvals where it doesn’t.
Automation and Attacker Infrastructure Edge
Many CNP fraud campaigns are automated. Bots can easily probe thousands of checkout attempts in minutes. These are often routed through residential proxy networks that make traffic appear to come from legitimate consumer devices. And it reduces the effectiveness of basic defenses such as simple IP reputation checks, geo-blocking, or static velocity rules.
For fraud teams, this creates an ongoing operational challenge. Continuously tuning defenses while balancing fraud prevention with checkout performance and customer experience is a perpetual struggle.
The Friendly Fraud Evidence Gap
First-party misuse is usually an intent question. Meanwhile, merchants can only provide transaction evidence.
Many lack automated evidence capture pipelines or fail to assemble the documentation before network deadlines. The result is low representment success rates and significant operational overhead.
New platforms like Chargeflow aim to close this gap by automating evidence collection, standardizing packages, and enabling pre-dispute monitoring.
Cross-Border Enforcement Realities
Fraudsters exploit global reach, targeting high-value markets from low-enforcement regions. Individual CNP cases rarely draw serious cross-border action. For instance, the Eurojust-coordinated global credit card fraud operation compromised 19 million credit cards across 193 countries, defrauding at least €300 million from both US/EU merchants, through fake subscriptions and CNP transactions.
Despite the scale, perpetrators initially went unpunished. It took such multi-agency coordination across Germany, Luxembourg, and others to ultimately dismantle the criminal ring and arrest 18 key actors.
With all these in mind, let’s dissect how top merchants prevent card-not-present fraud today.
Card-Not-Present Fraud Prevention Best Practices
For the modern merchant, the challenge is making sense of data in the milliseconds before a transaction is completed. Why? Because the biggest impact you can have is derisking that timeline to make the fraud business model less profitable than it currently is.
In a world of mass data breaches and AI-automated scams, the battle has moved to behavioral biometrics. Leading merchants are no longer just “blocking bad IPs.” They are tracking patterns in transactions that allow them to apply security as needed.
Here’s how it works:
To stay ahead, your technology stack must shift to dynamic intelligence. The ultimate best practice is to move the financial risk away from your bank account.
How Payment Gateways and Banks Address CNP Fraud Risks
Payment gateways and issuing banks operate with network-scale visibility that individual merchants rarely have. Understanding how they see and manage risk allows you to align your controls and reduce losses effectively.
How Gateways Think: Network-Wide Pattern Recognition
Gateways like Stripe, Adyen, and Helcim process millions of transactions across thousands of merchants. Because of this cross-merchant network capacity, they evaluate patterns to detect attacks that a single merchant might miss.
- Cards being tested on multiple sites are flagged or temporarily restricted across the gateway network. This is how Stripe prevented a new wave of 30 million carding attacks in 2025.
- Gateways transmit more than card numbers to issues; they include IP reputation, device fingerprints, and VPN/proxy detection, leading to enriched data streams.
Again, the gateway’s primary goal is network stability and compliance with card brands, not your revenue.
How Banks Think: Approval Optimization vs. Loss Prevention
Issuing banks make the final authorization decision based on cardholder data, balance, transaction amount, location, and internal risk checks. They generally lack the richer merchant signals, such as order history, device intelligence, or behavioral patterns.
To protect cardholders and minimize complaints, banks err on the side of caution. Mixed traffic may increase false declines, while consistent, low-risk traffic can improve approvals over time.
In other words, banks make decisions on card-level risk. Not merchant-level context, and their decision reflects protecting cardholders rather than maximizing your approvals.

What This Means for How to Respond to Card-Not-Present Fraud Attacks
Gateways and banks optimize for network health and cardholder protection, not your P&L. To reduce exposure:
- Pre-screen transactions: Ensure high-risk activity is filtered before authorizations to improve downstream approval rates. Excessive fraud or suspicious activity on your account can trigger gateway-enforced consequences, such as fines, increased scrutiny, or restrictions on your merchant account.
- Leverage liability shift: Since 3DS shifts liability to the issuer for successfully authenticated transactions, capture the ECI/CAVV values to document authentication and support the liability shift.
- Merchant-side intelligence: Tools like Chargeflow Prevent augment gateway and issuer defenses by analyzing repeat first-party disputes and other behavioral signals across multiple merchants.
Remember, gateways detect large-scale organized attacks; banks detect card-level anomalies. Your advantage comes from aligning merchant controls with their infrastructure to minimize losses, preserve conversions, and turn systemic asymmetry into a competitive edge.
Final Thoughts on Card-Not-Present Fraud
With card-not-present fraud accounting for roughly 73% or $12.5 billion of U.S. annual card fraud losses, it’s safe to say that every online merchant is a target. Fraudsters exploit mass credential acquisition, automated validation, account takeover, synthetic identities, and triangulation. This is often facilitated through AI-enabled bots and proxy networks.
Merchants bear financial, operational, and reputational risks, while cardholders face unauthorized charges and churn.
Effective defense aligns merchant controls with network intelligence. Pre-screen high-risk transactions, capture 3DS authentication values to leverage liability shifts, and deploy merchant-side intelligence to detect and block repeat abuse and behavioral anomalies. Treat card-not-present fraud as a systemic, industrialized threat. Use Chargeflow Prevent to respond with speed, precision, and layered controls.
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 20,000 merchants.
Related ARTICLES
Questions?
we’ve got answers.
Chargeflow collects data from dozens of third party signals, automatically. This allows for much more coverage and much better win rates because the evidence submitted is much more comprehensive and compelling.
Chargeflow collects data like order info, customer messages, and payment details. It builds a full dispute case for you, so you don’t have to lift a finger.
Yes! Chargeflow works with 50+ payment processors. That means one tool for all your chargebacks, no matter how you process payments.
You only pay a percentage of the revenue we help you recover. No upfront fees, no subscriptions — just success-based pricing.
Yes. Chargeflow is SOC 2 Type 2, GDPR, and ISO certified. We use top security standards to keep your data safe.
need more help?
Have a question? We’re here to help. Just hit the chat button to initiate a conversation with support.






















%201.svg)






































.png)


