Account Takeover (ATO) Fraud: Definition and How to Prevent It
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 15,000 merchants.
Account takeover fraud is when a fraudster gains access to a real customer account and uses it to make unauthorized transactions. Because the activity originates from a legitimate account, it often bypasses traditional fraud checks and later surfaces as a chargeback. Preventing ATO requires more than login security. It depends on detecting risky behavior before and after login, not just blocking access attempts.
Account takeover fraud doesn’t rely on stolen cards. It relies on access.
A fraudster logs into a real customer account using stolen or reused credentials. The payment method is already saved. The shipping details are already trusted. The transaction goes through without friction.
From the merchant’s perspective, it looks like a normal order.
The problem shows up later, when the customer disputes the charge.
Many merchants invest heavily in blocking fraud at checkout. ATO bypasses that layer entirely. The risk starts earlier, at login, and continues after access is granted.
Understanding how account takeover fraud works is the first step.
Preventing it requires looking beyond authentication and into behavior.
What is Account Takeover (ATO) Fraud?
Account takeover fraud is a type of fraud where a bad actor gains access to a legitimate customer account and uses it to perform unauthorized actions.
In ecommerce, that usually means placing orders, accessing stored payment methods, or using account balances. In other cases, it can involve changing account details, redeeming loyalty points, or accessing sensitive customer data.
The key difference from traditional fraud is access.
With stolen card fraud, the attacker uses the payment information directly. In an account takeover, the attacker uses the customer’s identity within an existing account.
That distinction matters.
Transactions coming from a logged-in account often pass fraud checks that focus on payment risk. The billing address matches. The device may not look suspicious enough to trigger a decline.
This is why account takeover fraud often manifests as an unauthorized transaction or chargeback, rather than a declined payment.
For merchants, that means the loss happens after fulfillment, not before authorization.
How Account Takeover Attacks Work
Account takeover attacks follow a simple pattern, but they’re effective because they blend into normal customer behavior.
It starts with credentials.
Fraudsters obtain login details through data breaches, phishing, or by testing reused passwords across multiple sites. This is known as credential stuffing. At scale, even a small success rate is enough.
Once they gain access, the account becomes the entry point.
From there, the attacker can:
- Place orders using saved payment methods
- Change shipping addresses
- Update account credentials to lock out the real customer
- Redeem stored value like gift cards or loyalty points
This is where most fraud systems lose visibility.

Many fraud controls are designed to evaluate transactions at checkout. But in an account takeover scenario, the attacker is already inside a trusted session. The transaction inherits that trust.
There’s no obvious signal that the activity is unauthorized.
The billing information matches. The account has a history. The behavior may only differ slightly from the customer’s usual pattern.
That’s why ATO is a post-login problem.
The risk doesn’t end when the user is authenticated. It begins there.
And by the time the real customer notices and contacts their bank, the transaction has already been completed and escalated into a dispute.
Common Techniques Used in Account Takeover Fraud
Account takeover doesn’t rely on a single method. It’s a combination of tactics that all aim to achieve the same goal: access.
The most common techniques include:
Credential stuffing
Attackers use lists of leaked usernames and passwords to attempt to log in across multiple sites. Because many users reuse credentials, even a low success rate creates access at scale.
Phishing
Customers are tricked into sharing login credentials via phishing emails, messages, or websites that mimic legitimate brands. Once credentials are captured, accounts can be accessed directly.
SIM swapping
Fraudsters take control of customers and contact support teams to gain access or reset credentials. This allows them to bypass SMS-based authentication and reset account passwords.
Social engineering
Attackers impersonate customers and contact support teams to gain access or reset credentials. This targets process weaknesses rather than technical ones.
Session hijacking
In some cases, attackers take over an active session without needing login credentials, often through malware or insecure networks.
Individually, these methods are well known. What makes them effective is consistency.
They don’t need to break systems. They take advantage of:
- reused passwords
- weak authentication flows
- gaps in account monitoring
- predictable support processes
Account takeover isn’t about bypassing security entirely. It’s about finding the weakest point in how access is managed and maintained.
Warning Signs of Account Takeover Activity (Before and After Login)
Most merchants focus on login attempts when thinking about account takeover. That’s only part of the picture.
Some of the most reliable signals appear after access is granted, when the account is already trusted.
These signals rarely appear in isolation. Risk increases when multiple signals occur within the same session.
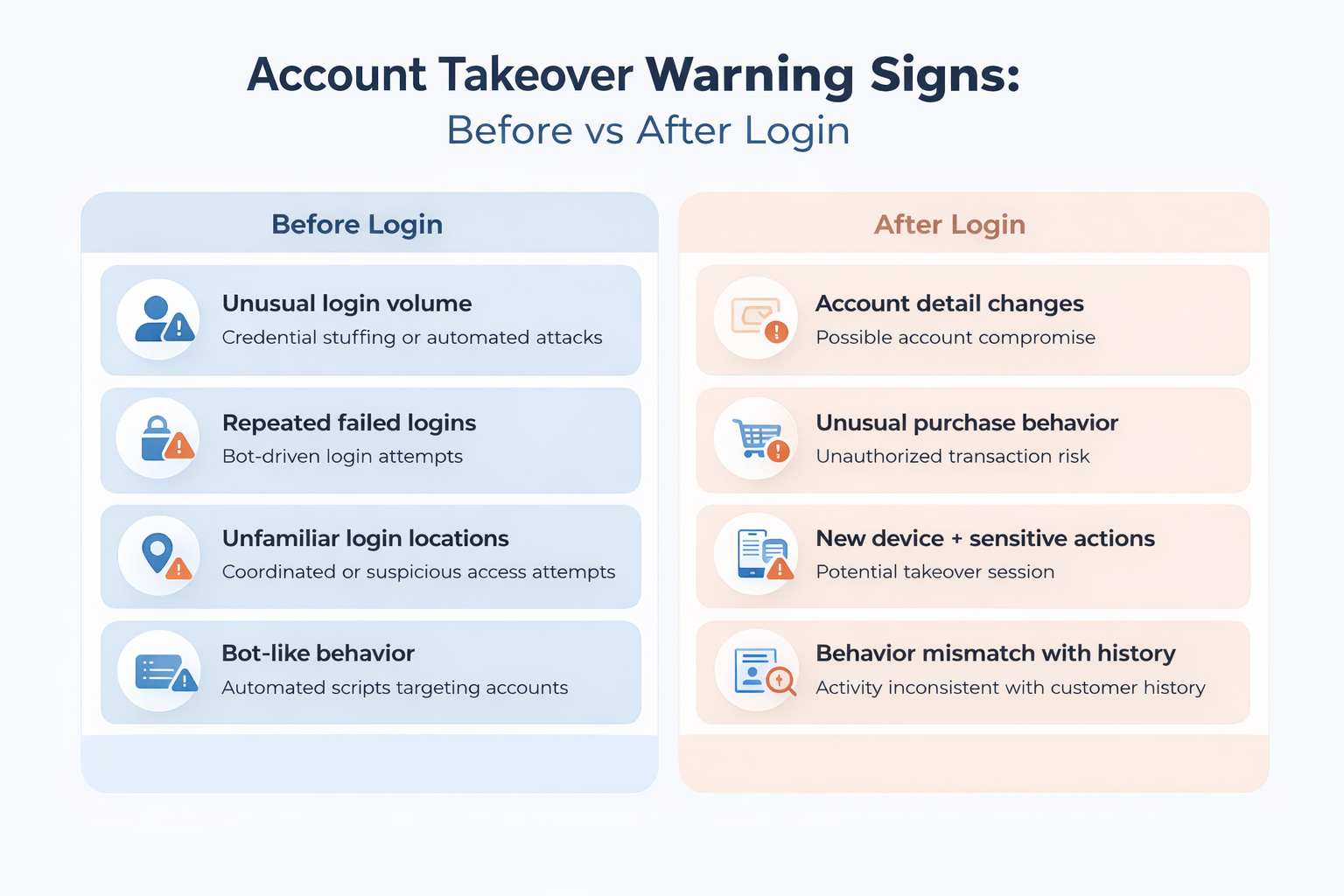
Before Login: Early Indicators
These signals point to attempts to gain access. They show where attacks are happening, but they don’t confirm compromise. Some login attempts will still succeed.
After Login: High-Risk Signals
This is where account takeover becomes visible, and where many systems fall short.
Sudden changes to account details, new devices followed by activity, or rapid sequences of actions often indicate that access has already been compromised.
Individual signals may appear normal on their own. Risk increases when multiple signals occur within the same session.
Most systems treat login as the checkpoint. In account takeover, login is the starting point. If detection stops there, the highest-risk activity goes unmonitored.
How to Prevent Account Takeover Fraud
Preventing account takeover isn’t about adding a single control. It’s about covering the full lifecycle of how access is gained and used.
Most merchants focus on login security. That’s necessary, but it’s not enough.
Account takeover risk spans three stages: before login, during authentication, and after access is granted.
Account takeover prevention works as a layered system across these three stages:
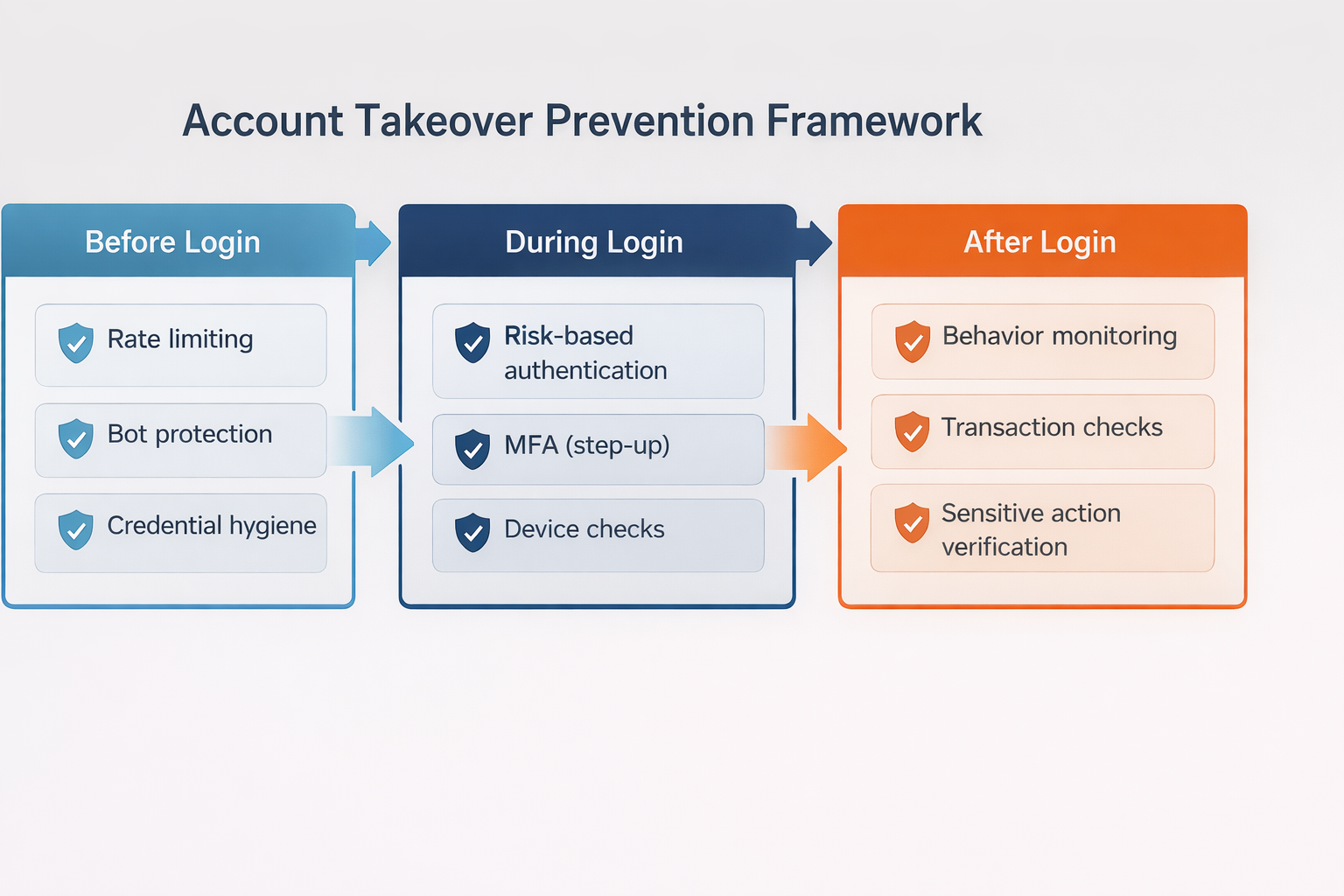
Most merchants overinvest in login security and underinvest in what happens after access is granted.
Before Login: Reduce Exposure
This is where most attacks begin.
Enforce stronger authentication standards
Encourage or require stronger passwords and limit credential reuse where possible. Weak or reused credentials are the entry point for most attacks.
Limit automated login attempts
Rate limiting and bot protection reduce the effectiveness of credential stuffing by slowing down or blocking repeated login attempts.
Monitor login patterns at scale
Spikes in login attempts across accounts often indicate coordinated attacks, even before individual accounts are compromised.
These controls reduce volume, but they don’t eliminate risk. Some login attempts will still succeed.
During Login: Evaluate Risk in Real-Time
Not every login attempt should be treated the same.
Use risk-based authentication
Evaluate factors like device, location, and behavior to determine whether additional verification is needed.
Apply step-up authentication selectively
Trigger additional verification, such as MFA, only when risk signals are present. This reduces friction for legitimate users while adding protection where it matters.
Track device and session consistency
New or unrecognized devices should not be treated the same as unknown sessions, especially for returning customers.
The goal here isn’t to block access entirely. It’s to challenge access when something doesn’t align.
After Login: Monitor Behavior Continuously
This is where most account takeover fraud actually happens.
Once access is granted, the session is trusted. Transactions, changes, and actions inherit that trust unless something interrupts it.
Watch for high-risk account changes
Updates to email, password, or shipping details immediately after login are strong indicators of compromise.
Monitor transaction behavior
Unusual order patterns, new shipping destinations, or rapid purchases can signal unauthorized activity.
Introduce step-up checks for sensitive actions
Require additional verification when customers attempt high-risk actions, not just at login.
Link behavior across sessions
Fraud often involves a sequence of actions. Looking at isolated events misses the pattern.
Prevention doesn’t stop at authentication. It depends on what happens after access is granted.
Account Takeover Detection and Protection Systems
Account takeover detection is built on signals.
No single signal confirms that an account has been compromised. Detection systems work by combining multiple signals across login, session, and transaction activity to identify behavior that doesn’t match the customer.
Detection systems rely on three types of signals: behavioral, device, and network, and account-level.
Behavioral Signals
These signals focus on how the account is used, not just how it is accessed.
- Changes in navigation patterns
- Unusual session behavior
- Rapid sequences of actions
- Activity that doesn’t match historical usage
Behavioral signals are often the most reliable because they reflect intent, not just access.
Device and Network Signals
These help identify whether the session matches the expected user environment.
- New or unrecognized devices
- IP address changes or inconsistencies
- Use of proxies, VPNs, or anonymized networks
These signals are useful, but not definitive. Legitimate users also switch devices and locations.
Account-Level Signals
These focus on changes within the account itself.
- Password or email updates
- Shipping address changes
- Multiple failed login attempts followed by success
These signals often appear right before fraudulent transactions occur.
Where Detection Systems Fall Short
Most account takeover detection systems are strongest at login.
They focus on:
- blocking credential stuffing
- identifying suspicious login attempts
- triggering MFA
That’s necessary, but it leaves a gap.
Once a login is successful, many systems reduce scrutiny. The session is treated as trusted, and monitoring becomes limited or inconsistent.
That’s where account takeover fraud happens.
Fraudsters don’t need to bypass every control. They only need to pass one checkpoint.
If detection is concentrated at login, it misses the sequence of actions that follows.
Detection Without Response Isn’t Enough
Detection alone doesn’t prevent loss.
Identifying suspicious behavior only matters if it triggers a response:
- step-up authentication
- transaction review
- temporary account restrictions
Without a response layer, detection becomes observation.
Effective protection depends on linking signals to action in real time, especially after login, when risk is highest.
Account Takeover Fraud and Chargebacks
Account takeover fraud doesn’t end at the login. It ends with a transaction the customer didn’t authorize.
From the merchant’s perspective, the order often looks legitimate. The account is real. The payment method is on file. The transaction passes standard fraud checks.
At that point, the transaction enters the chargeback process.
Most account takeover cases are classified as fraud by issuers. The cardholder claims they did not authorize the transaction, and the burden shifts to the merchant to prove otherwise.
That’s where the challenge becomes clear.
Unlike traditional fraud, where suspicious signals may exist at checkout, account takeover transactions inherit the trust of a valid account. Without strong authentication or clear evidence linking the customer to the transaction, these disputes are difficult to win through chargeback representment.
In many cases, the merchant has:
- A successful login
- A completed transaction
- Standard order and delivery data
But no definitive proof that the actual customer authorized the purchase.
That gap leads to losses.
Account takeover also overlaps with other dispute types. Some cases appear as unauthorized transactions. Others resemble friendly fraud, especially when account access is shared or unclear. From the issuer’s perspective, the distinction matters less than whether authorization can be proven.
For merchants, the outcome is the same.
Revenue is lost after fulfillment. The dispute counts toward chargeback ratios. Operational time is spent responding to cases with low recovery probability.
This is what makes account takeover different from most fraud categories.
The failure doesn’t happen at checkout. It happens earlier, when access is granted without enough context or control.
Preventing account takeover isn’t just about protecting accounts. It’s about reducing the number of transactions that turn into disputes in the first place.
Merchants that monitor behavior across the full account lifecycle, before login, during authentication, and after access, reduce both fraud exposure and downstream chargebacks.
That’s where the real control sits.
Account takeover doesn’t show up as fraud at checkout. It shows up later as unauthorized transactions and chargebacks.
If you’re seeing disputes tied to account activity, it’s worth looking at how those cases are handled after they happen.
See how Chargeflow helps merchants recover revenue from unauthorized transactions and ATO-related chargebacks.
Chargebacks?
No longer your problem.
Recover 4x more chargebacks and prevent up to 90% of incoming ones, powered by AI and a global network of 15,000 merchants.
Questions?
we’ve got answers.
Chargeflow collects data from dozens of third party signals, automatically. This allows for much more coverage and much better win rates because the evidence submitted is much more comprehensive and compelling.
Chargeflow collects data like order info, customer messages, and payment details. It builds a full dispute case for you, so you don’t have to lift a finger.
Yes! Chargeflow works with 50+ payment processors. That means one tool for all your chargebacks, no matter how you process payments.
You only pay a percentage of the revenue we help you recover. No upfront fees, no subscriptions — just success-based pricing.
Yes. Chargeflow is SOC 2 Type 2, GDPR, and ISO certified. We use top security standards to keep your data safe.
need more help?
Have a question? We’re here to help. Just hit the chat button to initiate a conversation with support.






















%201.svg)






































.png)








